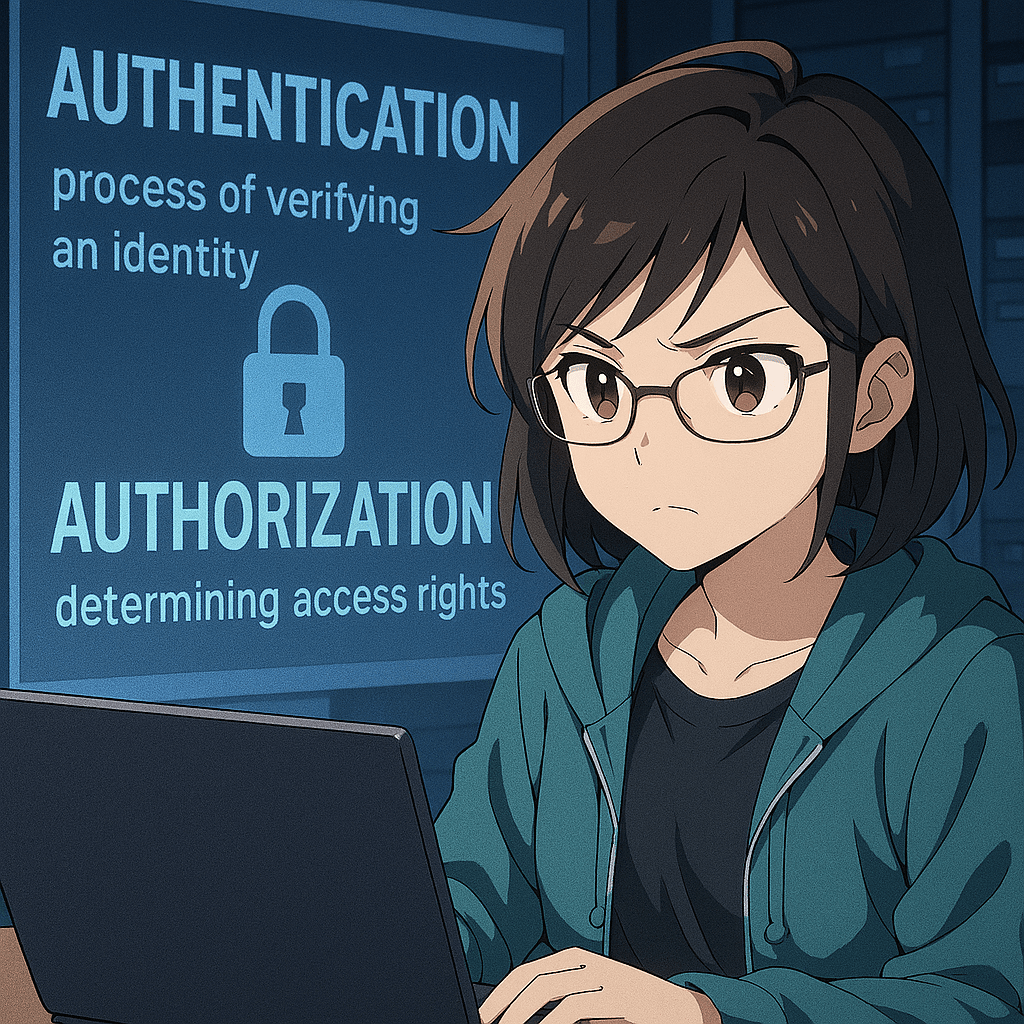
Authentication is the process of verifying that a user, device, or system is truly who or what it claims to be. It answers the question, “Who are you?” and relies on credentials such as passwords, PINs, biometrics (like fingerprints or facial recognition), security tokens, or digital certificates.
In essence, authentication establishes identity by checking provided information against stored, trusted data. Strong authentication mechanisms—such as multi‑factor authentication—combine multiple types of evidence to reduce the risk of impersonation or unauthorized access.
Without authentication, a system has no reliable way to distinguish legitimate users from attackers.
Authorization is the process of determining what an authenticated user is allowed to do within a system. It answers the question, “What are you permitted to access or perform?” Once a user’s identity has been confirmed, authorization rules decide which resources they can view, modify, or execute.
These rules are typically based on roles, permissions, or policies defined by administrators. For example, a regular user might be allowed to read certain files but not edit them, while an administrator may have full control.
Authorization ensures that even authenticated users operate only within the boundaries of their assigned privileges, protecting sensitive data and system integrity.
BitcoinVersus.Tech Editor’s Note:
We volunteer daily to ensure the credibility of the information on this platform is Verifiably True.
If you would like to support to help further secure the integrity of our research initiatives, please donate here: bc1q5qgtq8szqa6yy38tqpsyuk3hynq8zy3xvqhsvzecj8lnryrnzhmqsfmwhh
Leave a comment