Trending News
-

Reports tied to leaked internal documents said Amazon’s robotics team was aiming to automate 75 percent of company operations over time, avoid hiring about 160,000 U.S. workers by 2027, and trim fulfillment costs by about 30 cents per item. Wider projections attached to the same reporting said Amazon could avoid more than 600,000 U.S. hires…
-
Physicists at MIT have observed the “quantum jiggling” of electrons inside a superconducting material for the first time. Using a groundbreaking terahertz microscope that bypasses the traditional “diffraction limit” of light, the team was able to zoom in on the collective oscillations of the “superconducting gel.” This discovery had been theorized for decades but remained…
-

OpenAI is preparing a major shift in its consumer strategy with plans to launch a unified desktop super‑app that merges ChatGPT, a browser, and Codex‑powered development tools. The move follows an earlier stumble in online shopping integration, but the company is now positioning itself to compete directly with full‑stack productivity platforms. By consolidating AI chat,…
-

SoftBank Group, in a massive public-private partnership with the U.S. Department of Energy, has officially broken ground on the “Stargate” AI power and data campus in Piketon, Ohio. Located at a decommissioned uranium enrichment site, the project is staggering in scale: it aims for 10 gigawatts of computing capacity supported by a dedicated $33 billion…
-

Terafab, a large semiconductor manufacturing project backed by Elon Musk, is set to launch in Austin, Texas. The facility is a joint effort between Tesla and SpaceX and is designed to produce advanced chips for artificial intelligence, robotics, and space-based systems. The project is located near Tesla’s existing gigafactory in Austin. Musk aims to use…
-
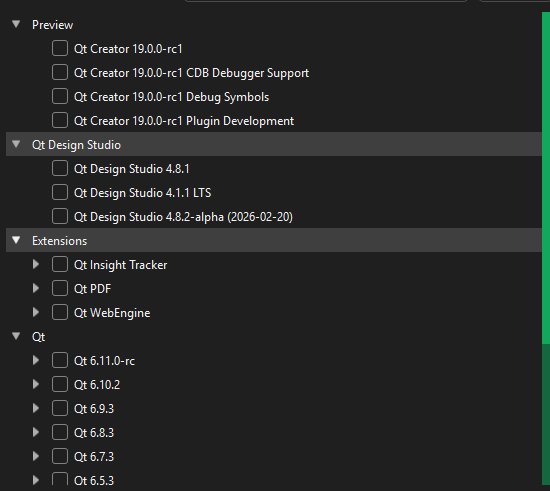
Qt is a professional software framework used to build graphical applications in C++ (and sometimes Python) that run on many operating systems such as Windows, Linux, and macOS. Instead of manually coding windows, buttons, charts, and graphics from scratch, Qt provides a large library of ready-made tools like QWidget, QPainter, buttons, text fields, and layouts…
-
Chinese researchers announced in February 2026 a breakthrough using reprogrammed stem cells to restore insulin production, successfully reversing type 2 diabetes in a patient after one year without medication, with early results also showing promise for type 1 cases. The therapy involves converting patient blood cells into insulin-producing islet cells transplanted into the body, avoiding…
-
BIOS stands for Basic Input/Output System. It is firmware stored on a chip on the motherboard that initializes hardware components and loads the operating system. BIOS interfaces are text-based, and users access them by pressing keys like DEL, F2, or ESC during system startup. BIOS uses Legacy Boot, has limited drive support (up to 2.2…
-
A REST API (Representational State Transfer Application Programming Interface) is a web interface that lets clients and servers communicate using simple, predictable rules based on standard HTTP methods like GET, POST, PUT, and DELETE. It treats data as resources identified by URLs, and each request represents a specific action on those resources, such as retrieving,…
-
In an era of groundbreaking developments in artificial intelligence (AI), the digital currency Bitcoin has been hailed by Bitcoin Activist Max Keiser as humanity’s hope amidst the rise of potentially threatening AI advancements. Keiser’s comedic yet poignant declaration came in response to concerns about a new model of AI, known as Q*, which some fear…
-
-
BitCluster, a Russian Bitcoin mining solutions provider, is set to launch a significant project in Ethiopia, which will revolutionize the cryptocurrency mining landscape. Scheduled to commence operations in January 2024, this venture involves the construction of a 120-megawatt (MW) data center in Addis Ababa, Ethiopia’s capital. The facility, spanning an impressive 30,000 square meters and…
-
You can download applications directly from the web using PowerShell on Windows. This guide explains how to use Invoke-WebRequest to download software, using Visual Studio Code as an example. Steps include opening PowerShell, defining the source URL, specifying the destination path, and executing the download command.
-

Originally Published in the summer of 2024 The power supply unit (PSU) is a fundamental component of the Bitcoin ASIC machine. The K9 PSU (pictured below) is a specific PSU for the K9 model ASIC machine. Generally, there are specific model PSU’s that are compatible with specific Bitcoin Mining Machines. 1. Materials needed:A. Drill (w/phillips…
-
-
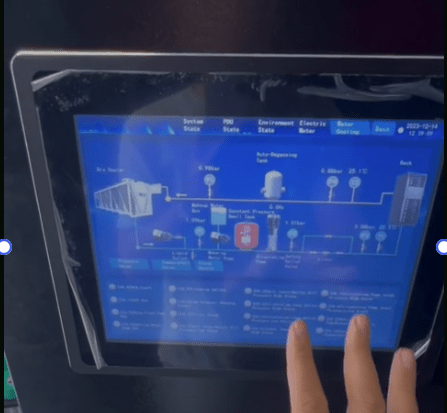
This article was originally published in January of 2024. Bitcoin mining has continued to evolve with groundbreaking advancements. Recently, Mingxu Wang, the (former) Director of Operations at Miningstore.com, explored the Green Hash Hydro facility, offering a glimpse into the promising future of hydro-cooling in bitcoin mining. This innovative approach is not just about enhancing the…
-
-
Modbus RTU (Remote Terminal Unit) is a widely used serial communication protocol developed by Schneider Electric in 1979 for industrial applications. It’s designed for communication between various devices such as programmable logic controllers (PLCs), sensors, and other industrial electronic devices. Modbus RTU uses a Commander/Executor architecture, where one device (Commander) initiates communication and controls one…
-
We know that Force is equal to mass times acceleration. A home has physical mass, structural strength, and load-bearing capacity. These properties give it force capacity in the physical sense. However, a home does not move and does not perform continuous work, so its velocity is effectively zero. As a result, its power output, in…
-
-
In computing, a script is a structured sequence of instructions written in a scripting language—such as Python, Bash, JavaScript, or PowerShell—that is interpreted and executed by a host environment at runtime rather than compiled into machine code beforehand. Scripts are designed to automate tasks, control software behavior, manipulate data, or coordinate system operations, often serving…
-
HTML input types are predefined modes of the element that determine what kind of data a user can enter and how the browser should validate, display, and interact with that field, enabling everything from plain text entry to specialized controls like dates, emails, numbers, passwords, file uploads, checkboxes, and radio buttons. Each type—such as text,…
-
HTML has a surprisingly rich history for something we now take for granted, and understanding where it came from makes its modern role much clearer. It began in the early 1990s when Tim Berners‑Lee created the first version as a simple markup system to share scientific documents across the emerging World Wide Web. Early HTML…
-
-
-
Border Gateway Protocol (BGP) is the core routing protocol of the global Internet, responsible for exchanging reachability information between large, independently operated networks known as Autonomous Systems (ASes). It is classified as an Exterior Gateway Protocol (EGP) and operates as a path‑vector protocol, meaning it selects routes based on entire AS‑paths rather than simple metrics…
-
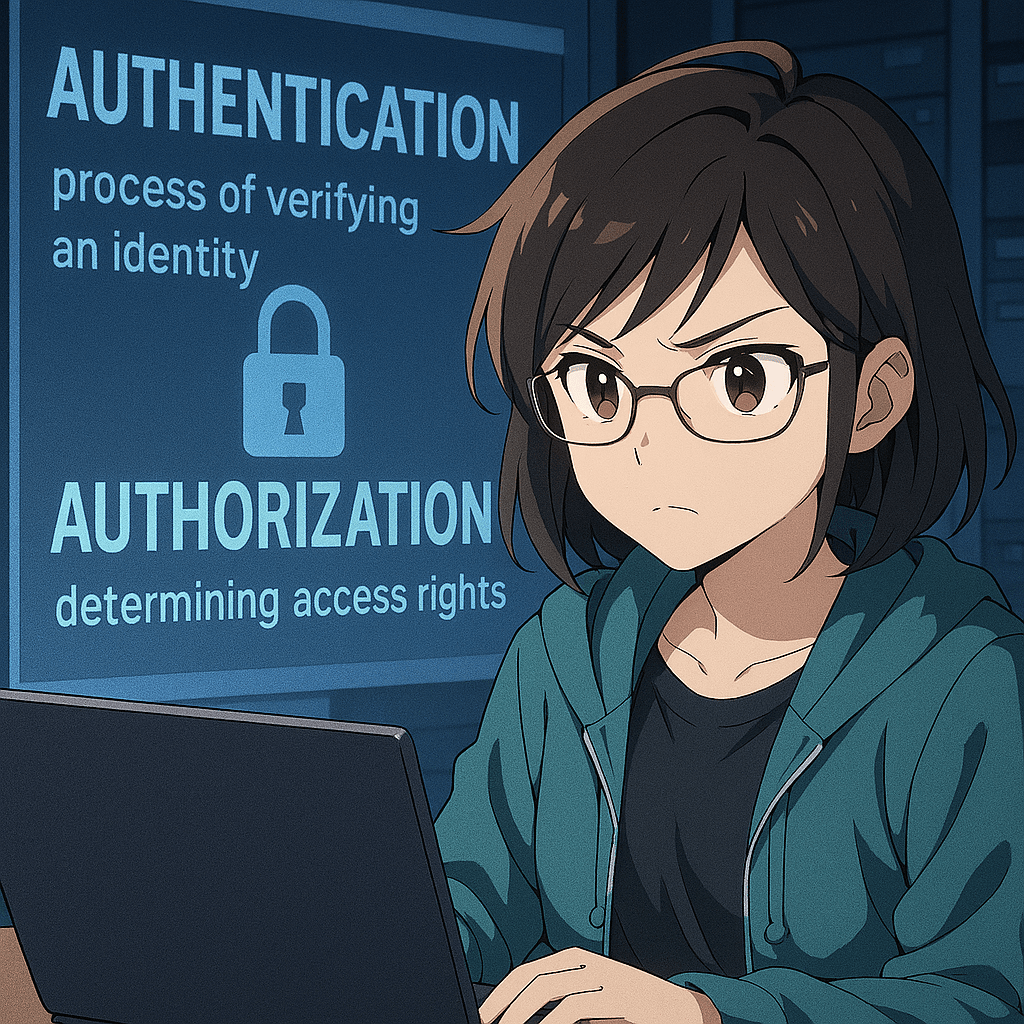
Information‑sharing partnership (often shortened in practice to “information partnership”) refers to a structured relationship in which two or more organizations agree to exchange security‑relevant information—such as threats, vulnerabilities, incidents, indicators of compromise, or best practices—in order to strengthen each participant’s overall security posture. It is built on the idea that no single organization has complete…
-
ICMP (Internet Control Message Protocol) is a network‑layer protocol used to send error messages, status information, and diagnostic signals between devices. It reports problems such as unreachable destinations or expired packet lifetimes and supports tools like ping and traceroute that test connectivity and measure network paths.” BitcoinVersus.Tech Editor’s Note: We volunteer daily to ensure the…
-
T568A and T568B are two valid Ethernet wiring standards that differ only in how the green and orange wire pairs are arranged, but this small change matters when matching existing infrastructure or ensuring consistent terminations. Both are approved under ANSI/TIA‑568.2‑D and will function identically as long as both ends of a cable use the same…
-
Installing Wireshark on Ubuntu is far easier through the terminal because Ubuntu already includes the correct Wireshark package in its official repositories. Instead of hunting through confusing alphabetical package indexes, mismatched versions, or multiple repository categories on the web, the terminal lets Ubuntu automatically detect your system version, architecture, and dependencies. A simple command like:…
-
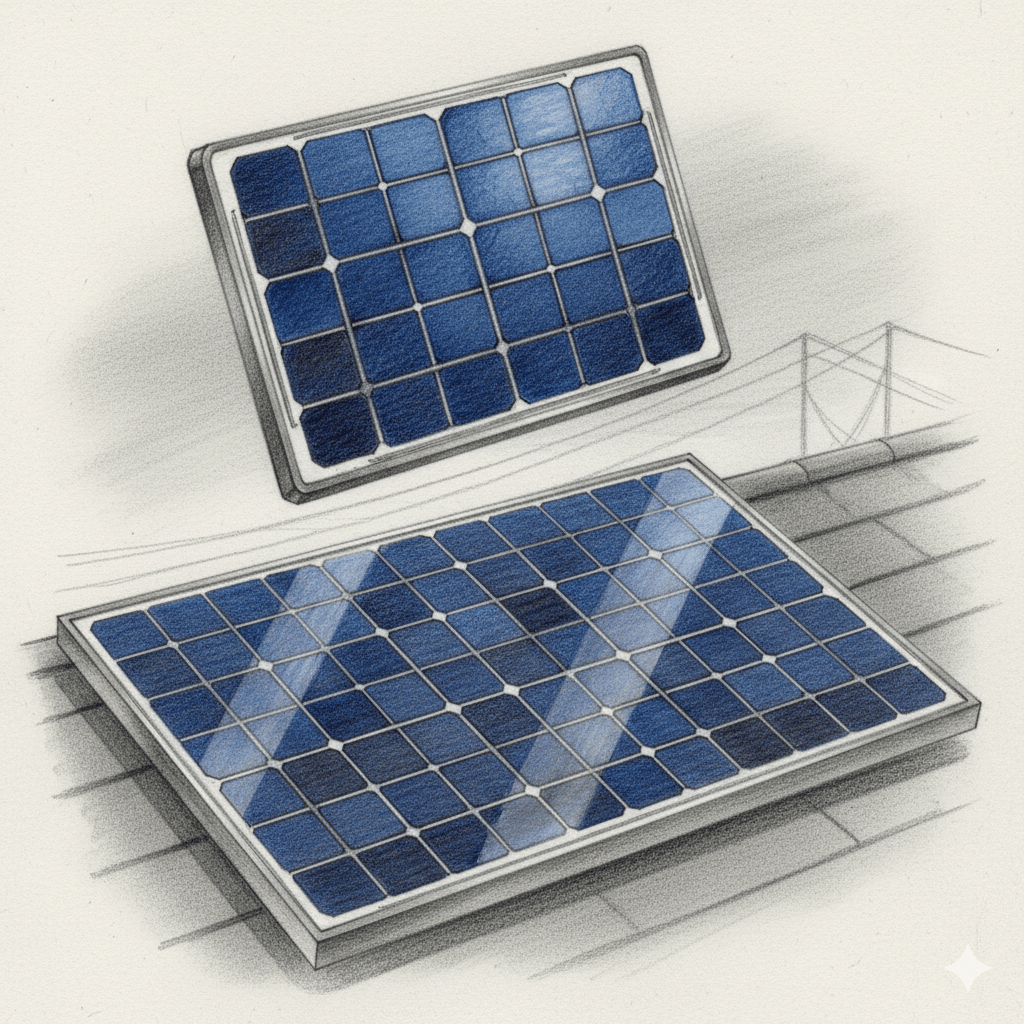
Installing a solar PV system can generate significant long‑term savings because it directly offsets the electricity you would otherwise purchase from your utility. According to EnergySage, the average U.S. homeowner saves about $57,000 over 25 years by going solar, reflecting both reduced monthly bills and the compounding effect of rising utility rates. These savings accumulate…
-
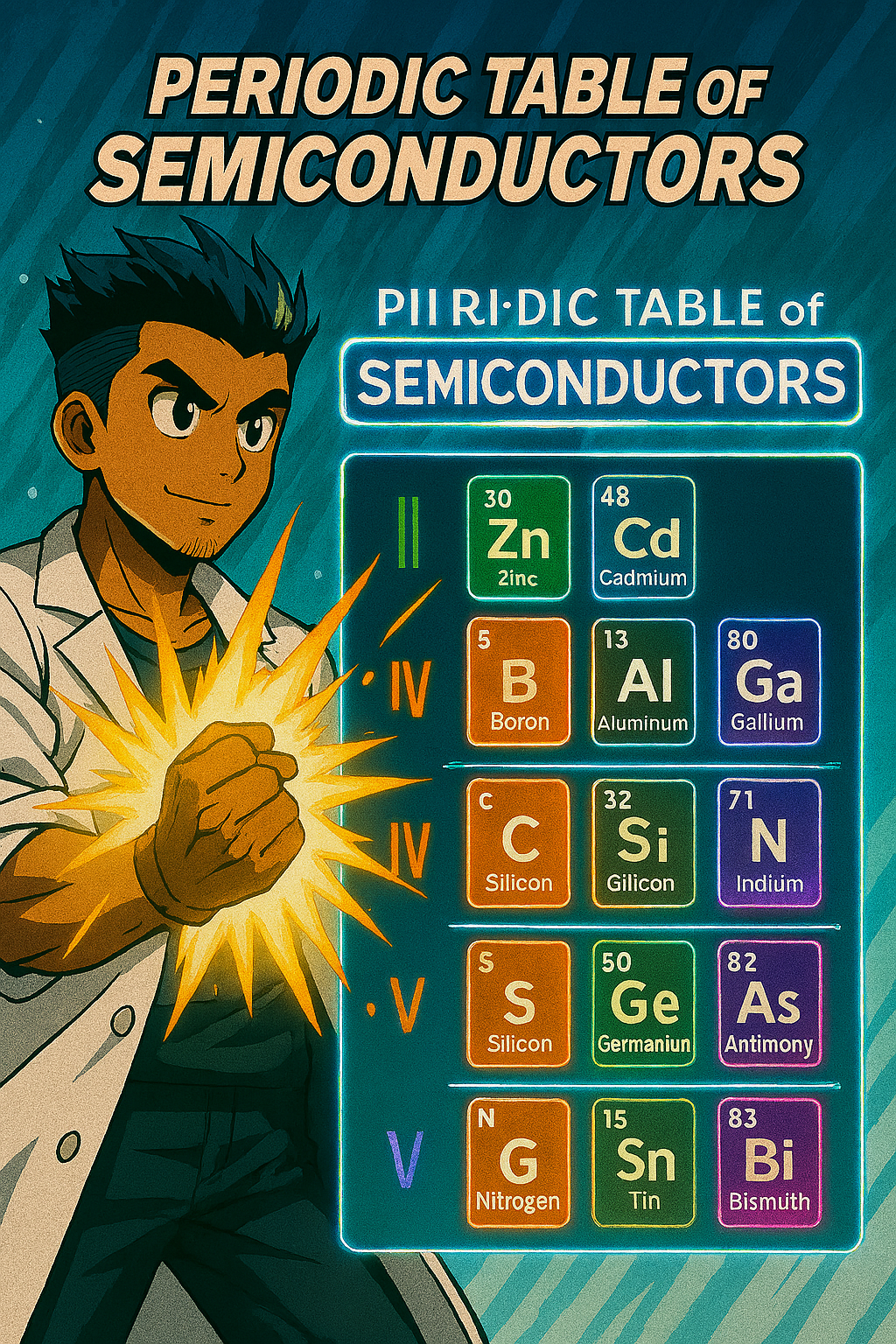
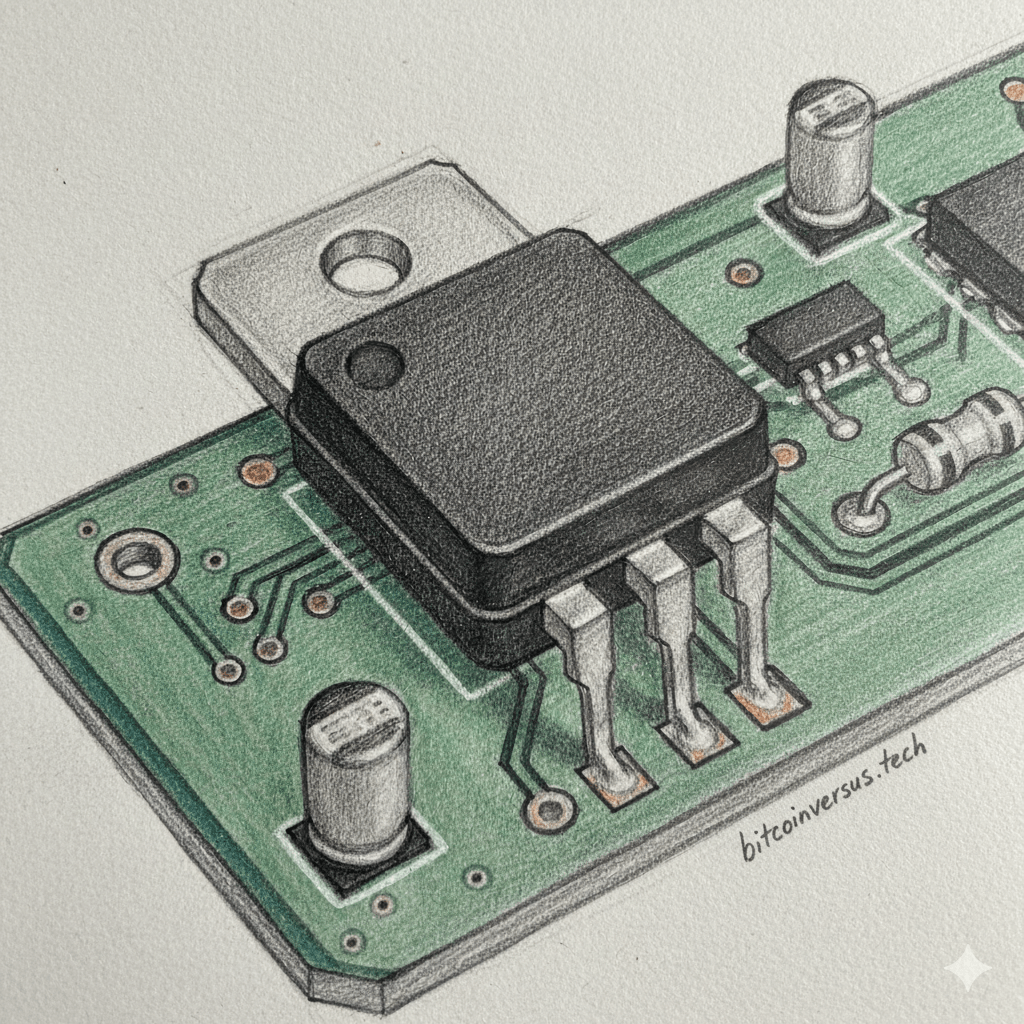
Semiconductors can be classified according to their position in the periodic table, and this classification helps in understanding their properties and applications. Group IV elements such as silicon, germanium, and tin are elemental semiconductors, with silicon being the most widely used due to its stability and abundance. Group VI elements like selenium and tellurium also…
-
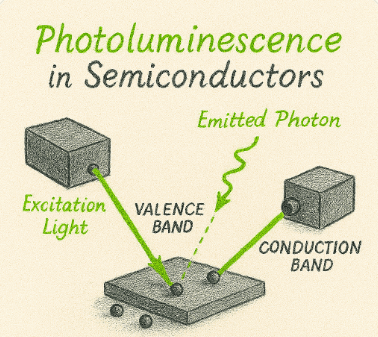
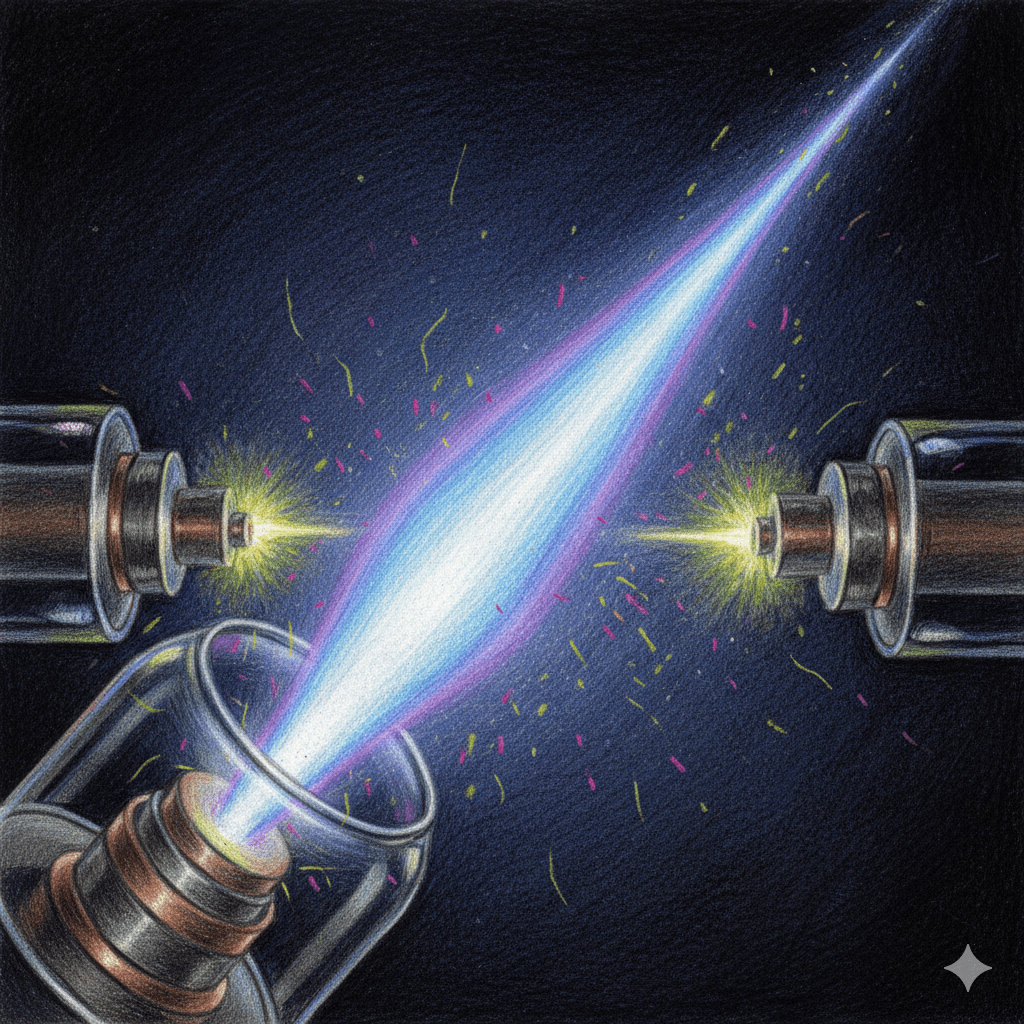
Photoluminescence is a fundamental optical process in which a material emits light after absorbing photons, typically at a longer wavelength than the excitation source. When light of sufficient energy strikes a material, electrons are promoted from lower-energy states (often the valence band) to higher-energy states (such as the conduction band). As these electrons relax back…
-
Bremsstrahlung, meaning “breaking radiation” in German, is the electromagnetic radiation produced when a charged particle, typically an electron, is decelerated or deflected by the electric field of an atomic nucleus. As the electron slows down or changes direction, the lost kinetic energy is emitted as photons, often in the X-ray range. This process is a…
-
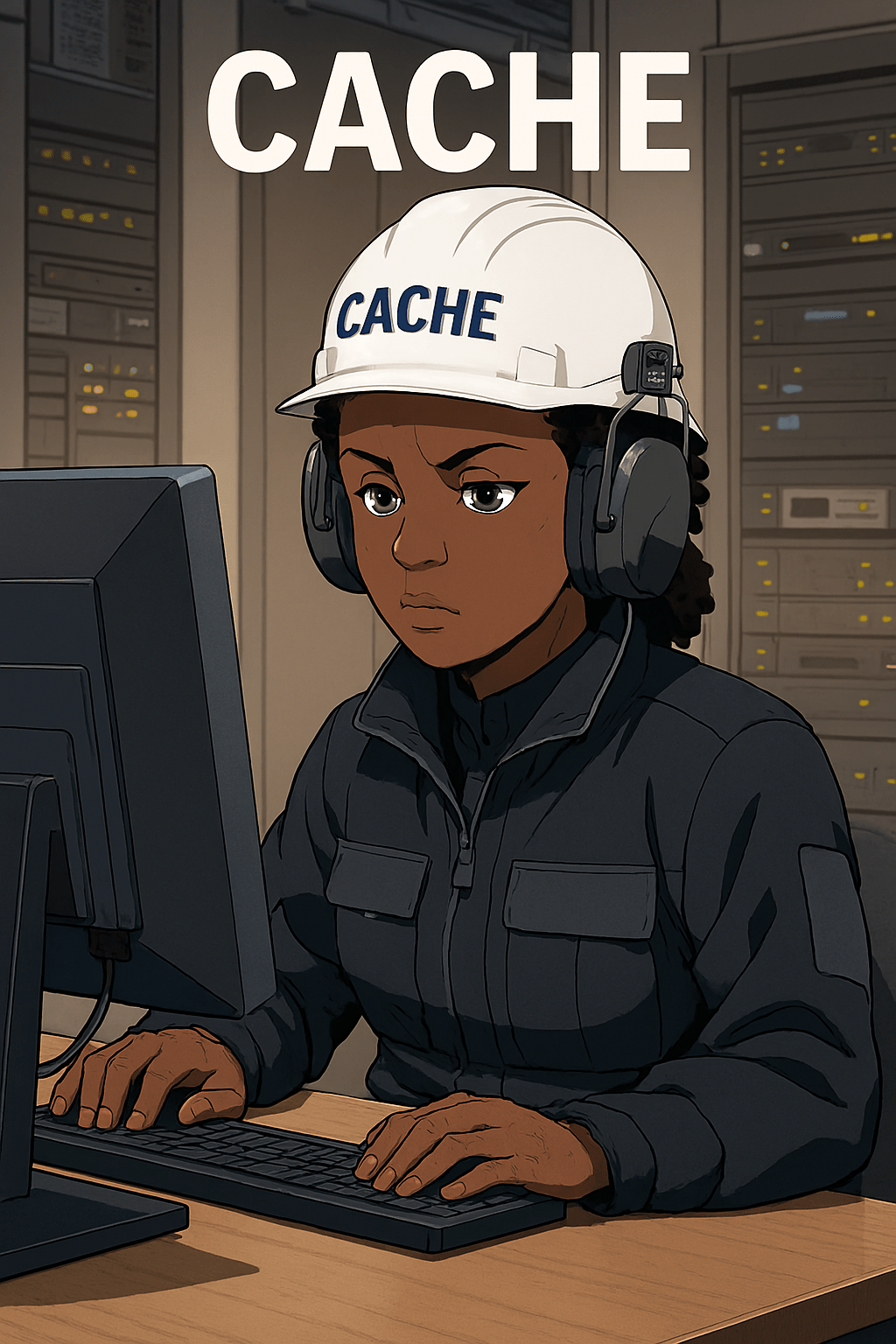
Cache is a high‑speed data storage layer designed to keep frequently accessed information close to the processor, dramatically reducing the time it takes to retrieve that data. Instead of reaching all the way out to main memory or even slower storage, the CPU first checks the cache. When the requested data is already there, known…
-
A stream cipher is a form of symmetric encryption that protects data by processing it in a continuous flow, usually one bit or one byte at a time. Instead of working with large, fixed‑size blocks of data, a stream cipher generates a keystream—a long sequence of pseudorandom bits—derived from a secret key and sometimes an…
-
Virtualization relies on three foundational requirements: equivalence, resource control, and efficiency. Equivalence means that a program running inside a virtual machine should behave exactly as it would on real hardware, with no modifications required. Resource control ensures that the virtual machine monitor (VMM) or hypervisor has full authority over hardware resources, preventing virtual machines from…
-
The fetch-decode-execute cycle (also known as the fetch-decode-perform cycle or simply the instruction cycle) is the fundamental process by which a computer’s central processing unit (CPU) executes program instructions stored in memory. It begins with the fetch phase, where the CPU retrieves the next instruction from main memory using the address stored in the program…
-
The three pillars of information security -Confidentiality, Integrity, and Availability (CIA Triad)—form the foundation of protecting data and systems. Together, the CIA Triad provides a balanced framework: confidentiality protects privacy, integrity preserves trust, and availability guarantees usability. Organizations must continuously manage trade-offs among these pillars to maintain secure, reliable, and effective information systems. BitcoinVersus.Tech Editor’s…
-
A string inverter is a centralized power conversion device used in solar energy systems to transform direct current (DC) electricity generated by multiple photovoltaic (PV) panels into alternating current (AC) electricity suitable for use in homes, businesses, or the electrical grid. In this configuration, solar panels are electrically connected in series to form a “string,”…
-
Common number bases in computing are essentially the languages computers speak. Here’s a quick rundown: Binary (Base 2): Uses 2 digits (0, 1) and is the native language of computers, representing data as electronic signals (on/off). It’s the foundation of all computing and is used to write machine code. Decimal (Base 10): Uses 10 digits…
-
Solar inverters are essential devices in photovoltaic (PV) systems that convert the direct current (DC) electricity generated by solar panels into alternating current (AC) electricity, which is compatible with household appliances and the utility grid. They serve as the “brain” of a solar energy system, not only enabling energy conversion but also managing system performance,…
-
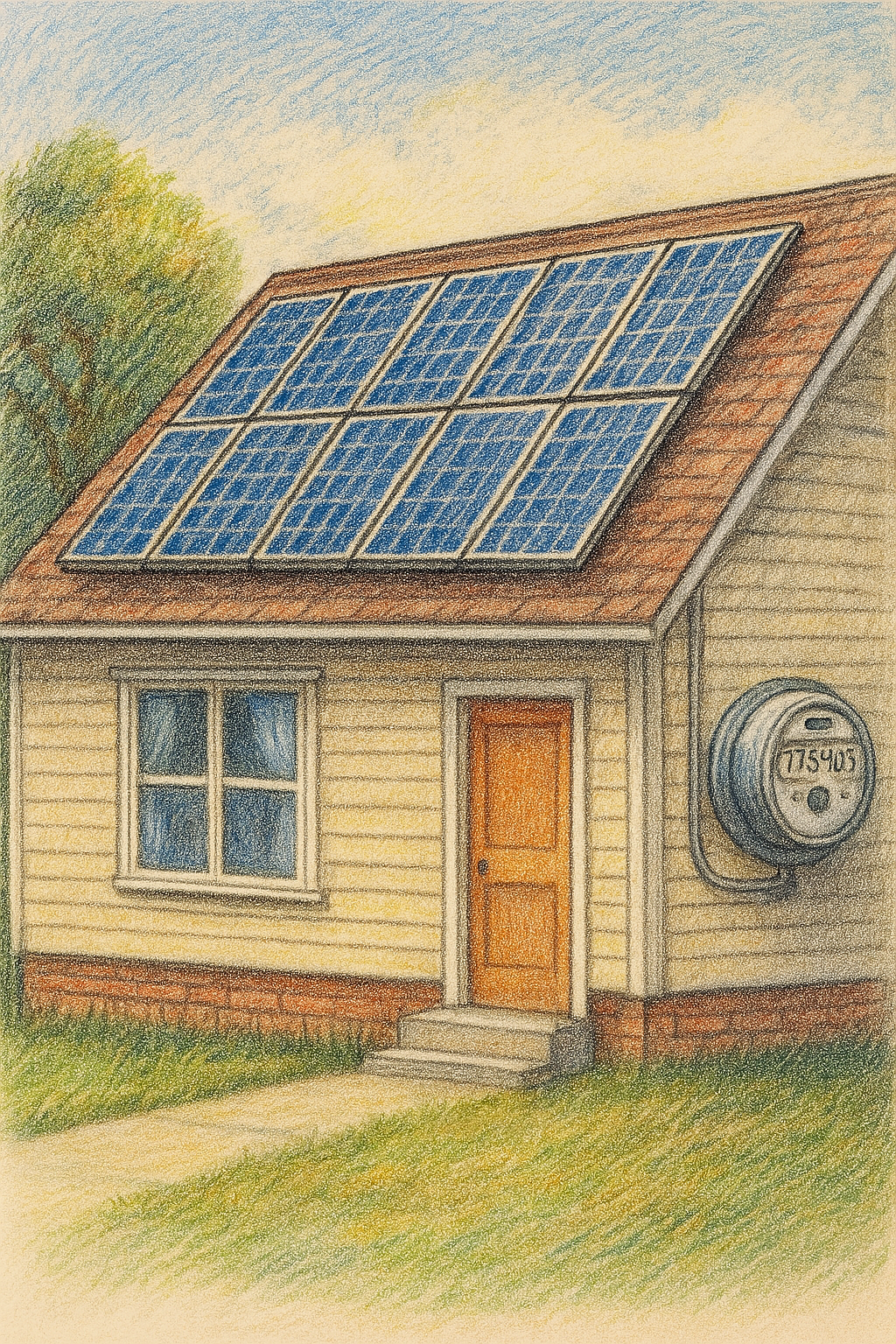
Net metering is a billing arrangement in which the electricity produced by a solar photovoltaic (PV) system is first used to meet the on-site demand, and any surplus is exported to the utility grid. When this happens, the customer earns credits that can be applied against the electricity they consume from the grid at times…
-
PV modules, commonly known as solar panels, are the foundational units of solar energy systems. Each module contains numerous photovoltaic cells—usually made from monocrystalline or polycrystalline silicon—that work together to generate electricity through the photovoltaic effect. These cells are embedded between layers of protective materials: a front layer of tempered glass for durability and light…
-
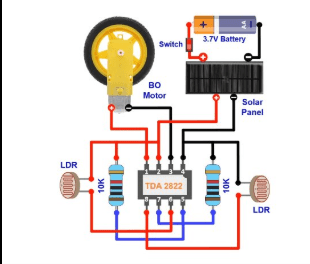
This DIY electronic solar tracker is a clever and simple project that helps a small solar panel automatically follow the sun to capture the maximum amount of sunlight throughout the day. The schematic illustrates a simple automatic solar tracker that uses two light-dependent resistors (LDRs) to sense the direction of the brightest sunlight and drive…
-
A lattice atom refers to an atom that occupies a regular, repeating position within the crystal lattice of a solid material. In crystalline solids, atoms are arranged in a highly ordered structure known as a lattice, where each atom is situated at a specific point defined by the geometry of the unit cell. These lattice…
-
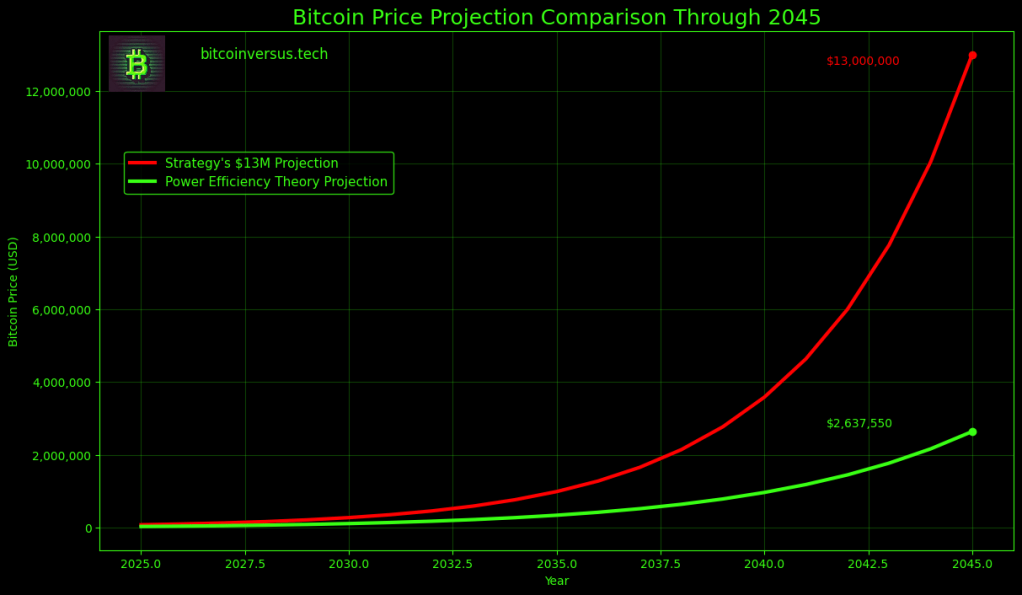
Michael Saylor, executive chairman of Strategy, has forecast that Bitcoin could reach $13 million per coin by 2045, implying a network value approaching $280 trillion. In interviews with CNBC, Saylor argued that Bitcoin could capture roughly 7 percent of global capital markets, far above its current share of global wealth. His projection assumes large scale…
-
In semiconductors, a substrate is the foundational material—typically a thin, flat wafer of crystalline silicon or another semiconductor—that serves as the base upon which electronic devices and integrated circuits are built. The substrate provides mechanical support and establishes the crystal lattice structure that determines the electrical properties of the devices fabricated on it. During manufacturing,…
-
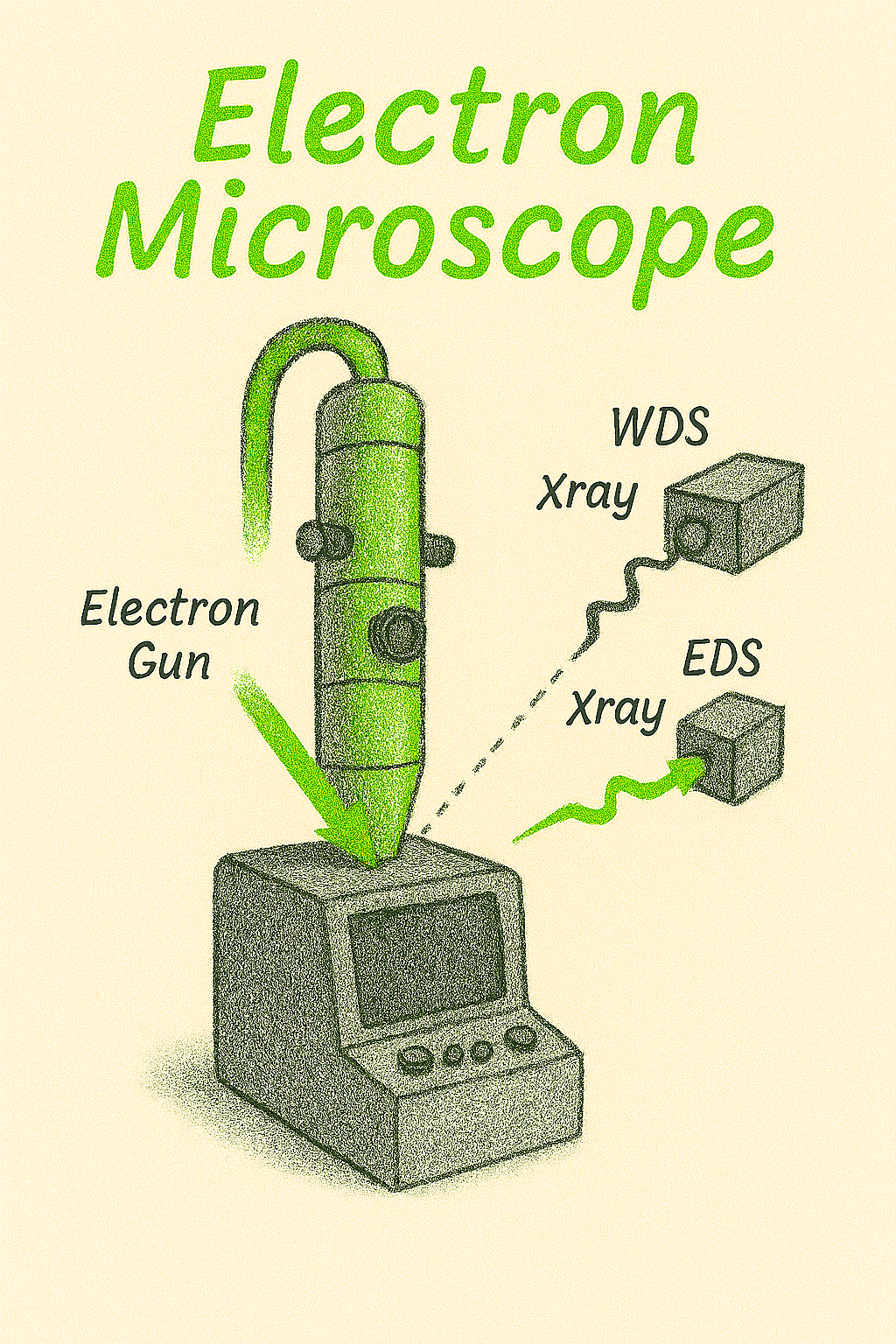
Wavelength Dispersive Spectroscopy (WDS) is an analytical technique used in electron microscopy to determine the elemental composition of materials with high precision. In WDS, characteristic X-rays emitted from a sample are diffracted by a crystal and separated based on their wavelength before being detected. This method provides excellent spectral resolution, allowing researchers to distinguish between…
-
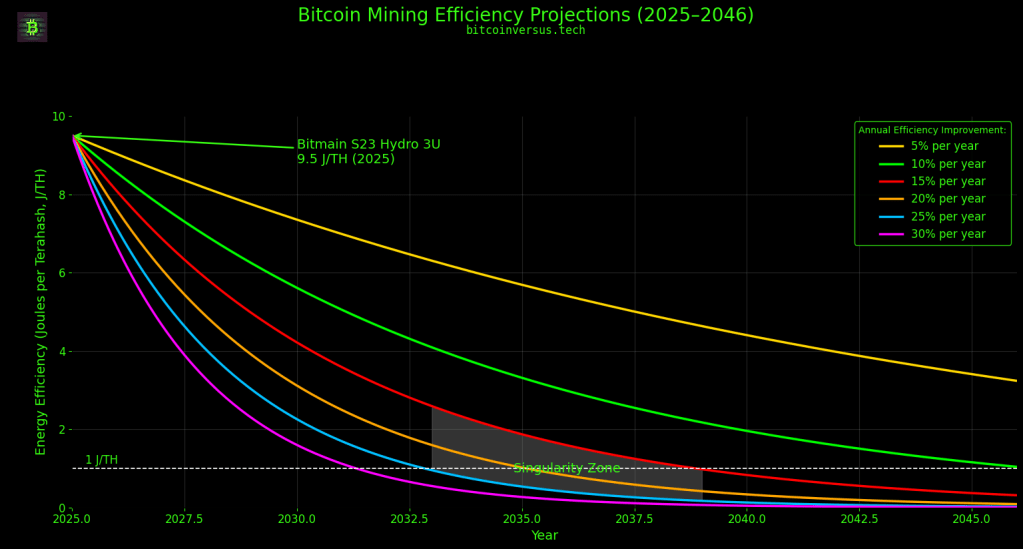
It will take some time to figure out if tracking the energy efficiency and computational power progression of the bitcoin ASIC Mining Machine has anything to do with the anticipated value of bitcoin. Under the current parameters of the model, Power Efficiency Theory suggests that Bitcoin could approach roughly $2-$3 million per coin by 2045,…
-
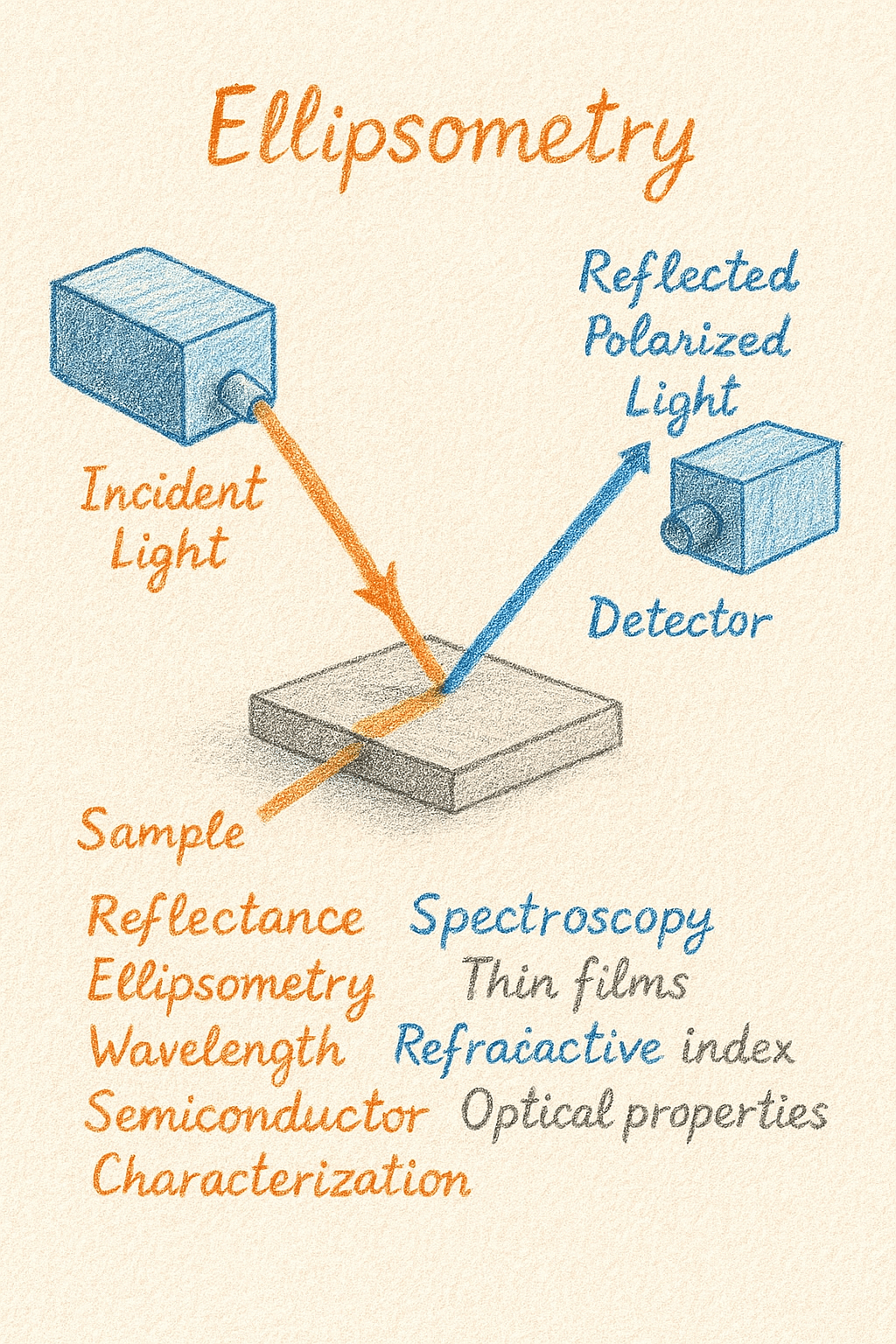
Ellipsometry is an advanced optical technique used to characterize thin films and surfaces by analyzing changes in the polarization of light upon reflection or transmission. In practice, a beam of polarized light is directed at a material, and the reflected or transmitted light undergoes a change in polarization that is measured as two parameters: the…
-
How do you anticipate failure? How can one prepare for something bad that’s going to happen, but you just don’t know when? A spiritual shield is a healthy start. But what does that spiritual shield look like on the ground in real life? Perhaps your spiritual shield on the ground looks like an if-then, sequential…
-
Solar cell roughness characterization is the process of analyzing and quantifying the surface texture of photovoltaic materials to understand how microscopic topographical features influence optical and electrical performance. The surface of a solar cell—whether crystalline silicon, thin-film, or emerging materials like perovskites—plays a critical role in determining how light interacts with the device. Controlled roughness…
-
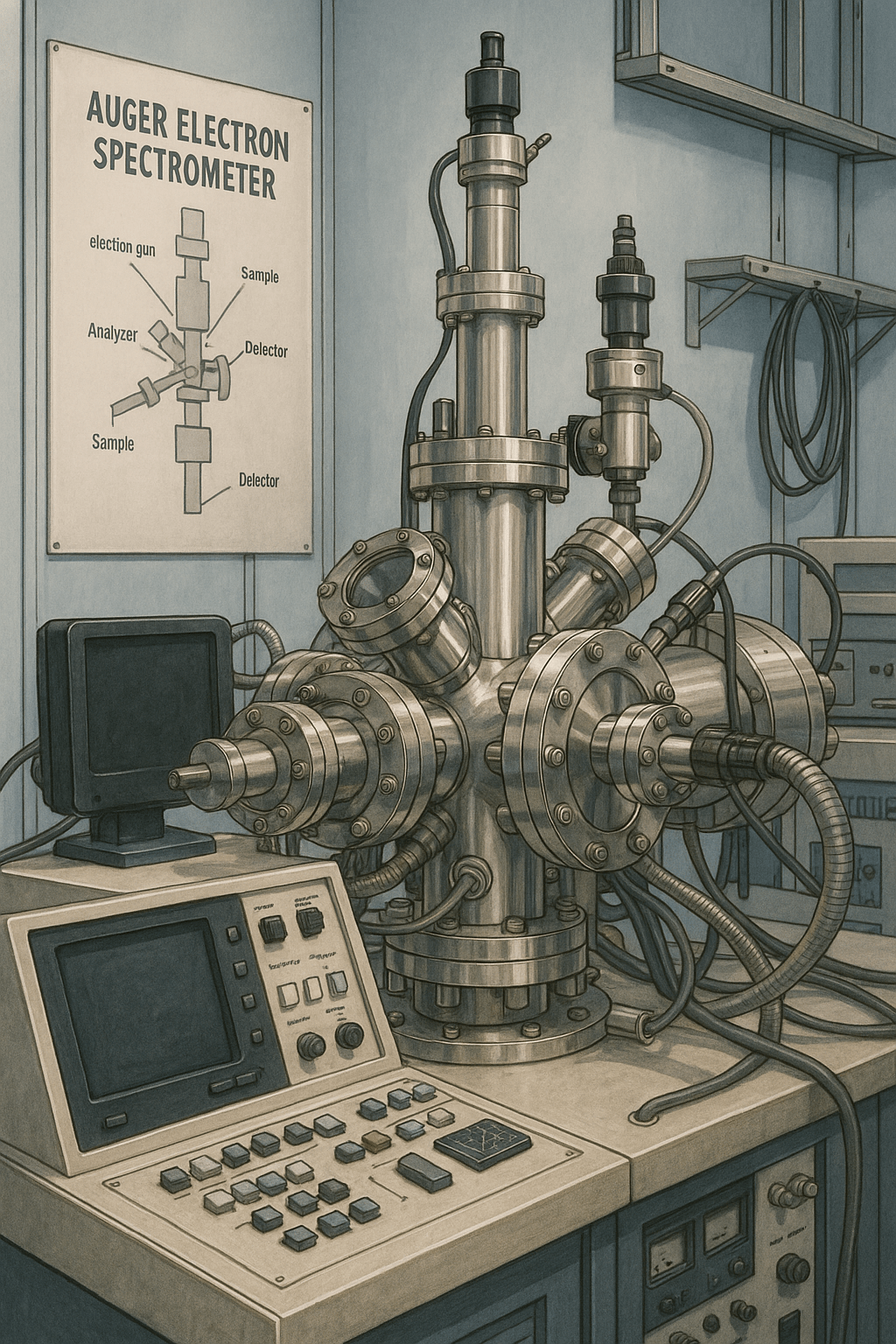
Auger electron emission is a physical process that occurs when an atom with a vacancy in one of its inner electron shells undergoes relaxation. After the removal of a core electron—typically by an incident high-energy electron or X-ray photon—an electron from a higher energy level drops down to fill the vacancy. The excess energy released…
-
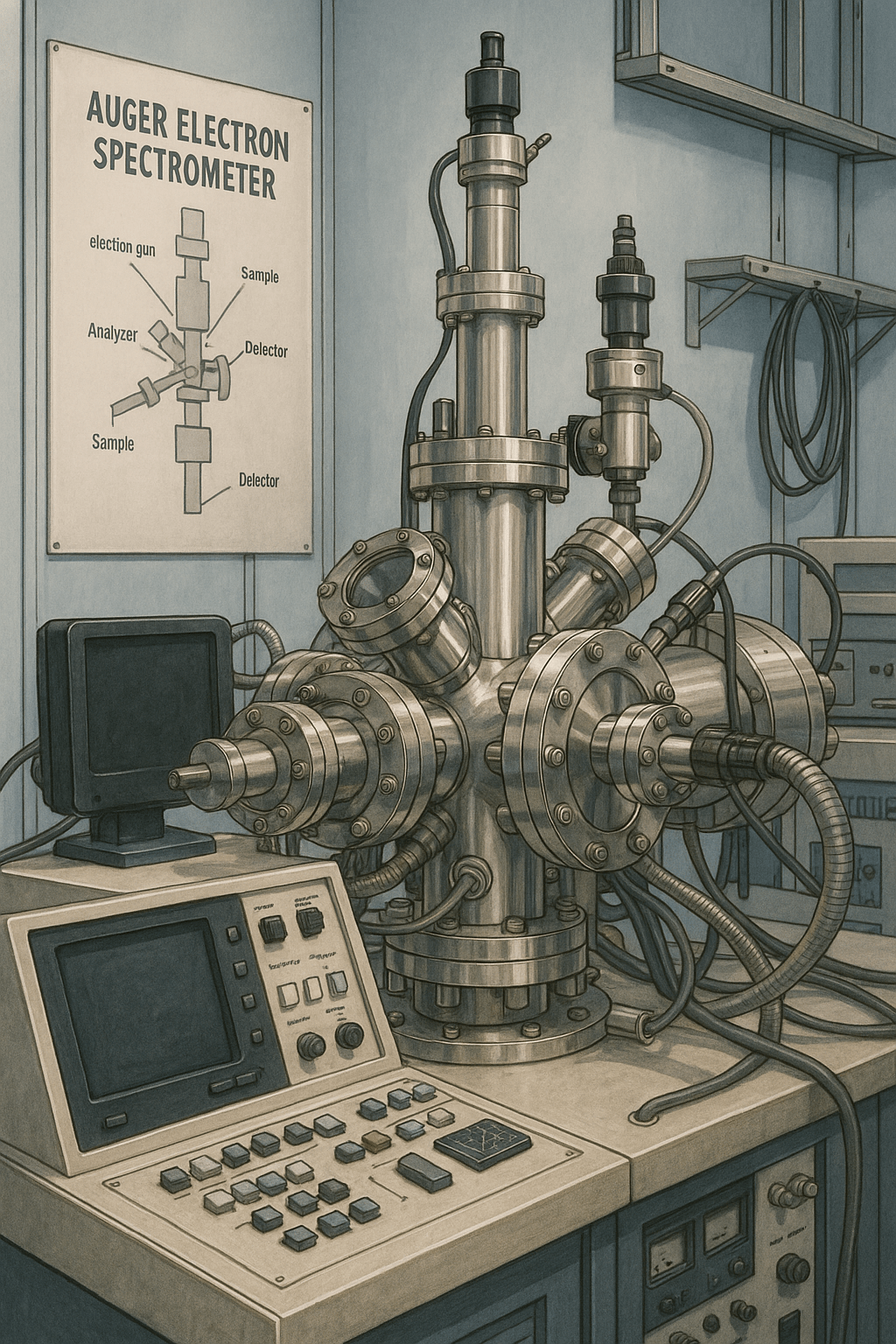
Auger Electron Spectroscopy (AES) is a powerful surface-sensitive analytical technique widely used in materials science to investigate the elemental composition of the outermost atomic layers of a sample. Unlike bulk characterization methods, AES focuses specifically on the top few nanometers of a material, making it invaluable for studying thin films, coatings, and surface modifications. The…
-
SIMS (Secondary Ion Mass Spectrometry) instrumentation is designed to analyze the surface composition of materials by detecting ions ejected from the surface. The system includes a primary ion source that fires a focused beam of ions (like gallium or cesium) onto the sample. This bombardment knocks atoms and molecules off the surface, some of which…
-
Polycrystalline silicon, often called poly-si, is a special material used to build the tiny pathways inside computer chips. Its main job is to control the flow of electricity, and a key property it has is called resistance. Resistance is how much a material slows down or fights against the electric current. Think of it like trying…
-
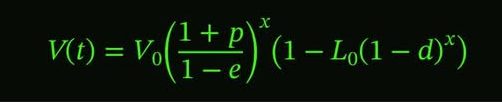
Let me be very clear. Power Efficiency Theory seeks to measure verifiable energy metrics directly related to the bitcoin protocol. I contend that the individual system (the ASIC machine) is the most reliable way to measure the anticipated value of bitcoin. You can collect metrics using the Individual systems or the entire system, but there…
-
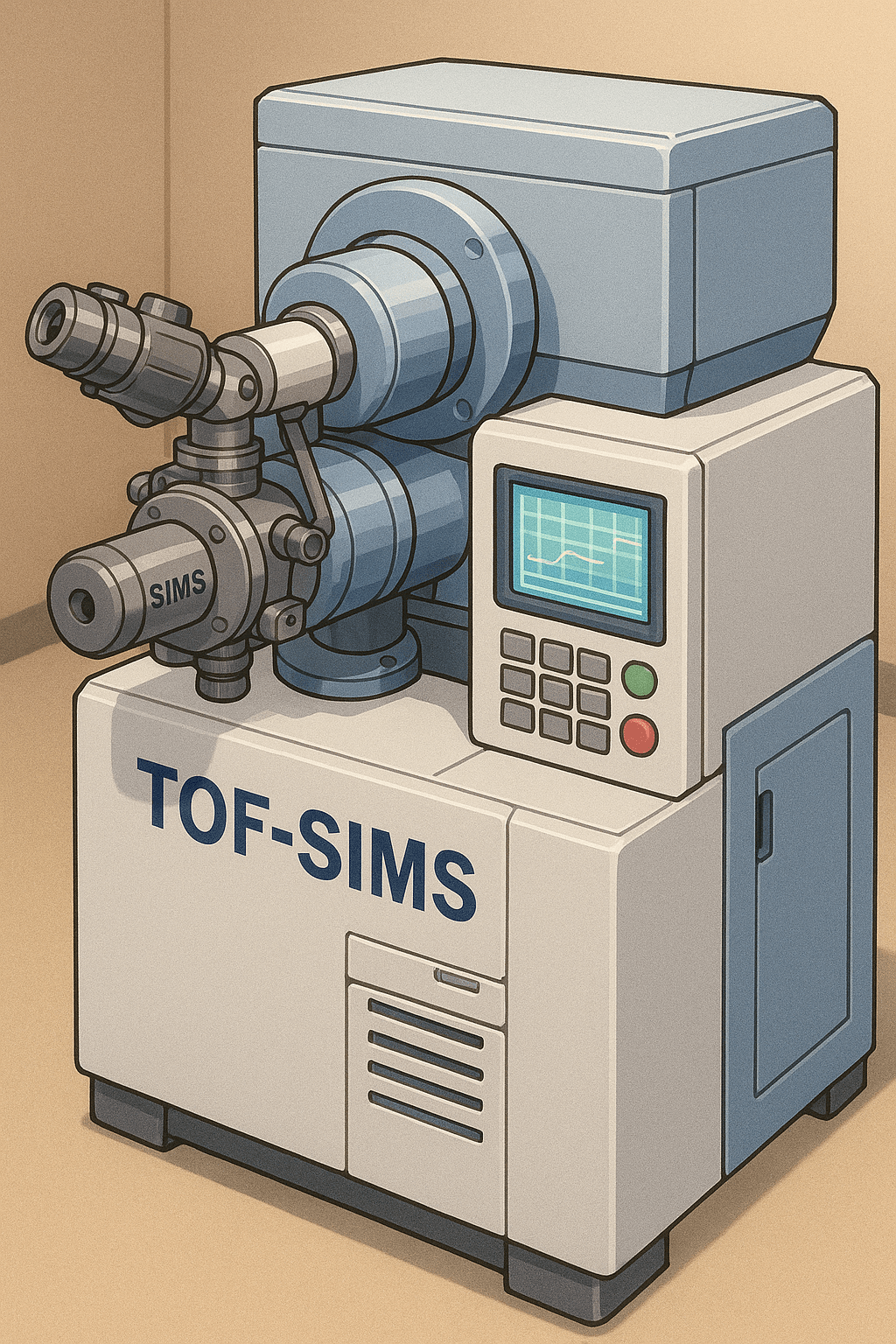
Time-of-Flight Secondary Ion Mass Spectrometry (TOF-SIMS) is a powerful technique used to analyze the surface of materials by detecting the chemical composition of just the outermost layers. The technique allows for analysis of a chemical structure in 3D with nanoscale resolution. In this method, a sample is bombarded with a focused beam of primary ions.…
-
The solar energy industry traces its roots to nineteenth century scientific discoveries, beginning with the photovoltaic effect identified by Edmond Becquerel in 1839 and early selenium based cells in the late 1800s. It did not become a modern commercial sector until Bell Labs created the first practical silicon solar cell in 1954, which initially found…
-
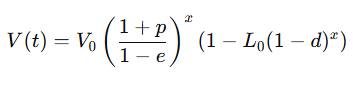
Power Efficiency Theory (P Theory) models the long-term valuation trajectory of a technological system by measuring the combined progression of computational power and energy efficiency. In Bitcoin mining hardware, these two variables are represented by hashrate output and energy efficiency measured in joules per terahash (J/TH). As computational power increases and energy required per unit…
-
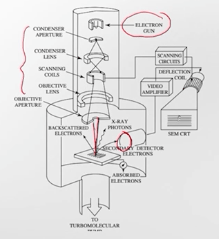
Scanning Electron Microscopy, or SEM, is a way to take very close‑up pictures of tiny things by shooting a thin beam of electrons onto a sample and moving the beam back and forth like a scanner. When the electrons hit the surface, they knock out other electrons and sometimes cause the material to emit X‑rays;…
-
A key logger (short for “key logger”) is a software or hardware tool that records the keys pressed on a keyboard, capturing the characters typed by a user. The collected data can include passwords, messages, personal information, and any other text entered on the device. Key loggers are often used covertly to monitor activity without…
-
Electron beam characterization involves using a focused beam of electrons to probe and analyze materials at very fine scales. Techniques such as scanning electron microscopy (SEM) and transmission electron microscopy (TEM) rely on the interaction between electrons and the atoms in a sample to reveal details about surface morphology, internal structure, and even chemical composition.…
-
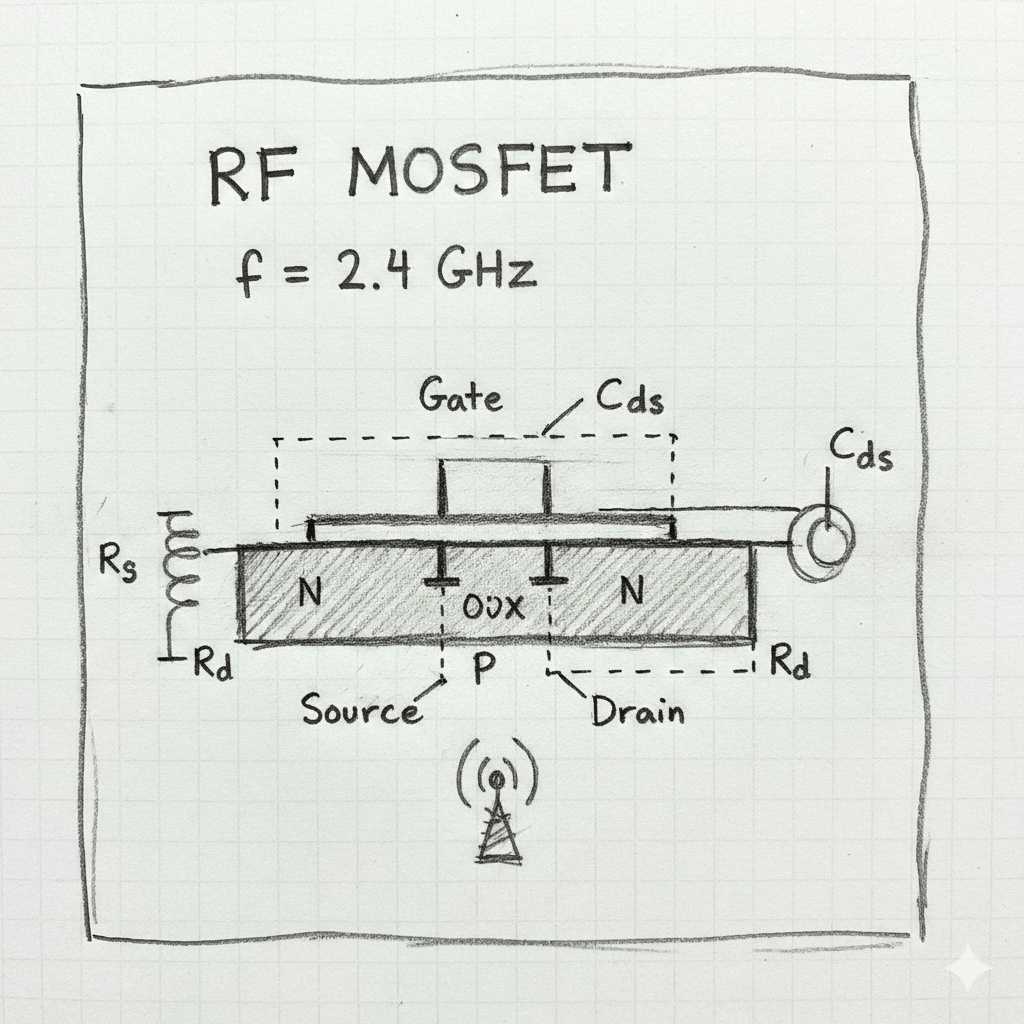
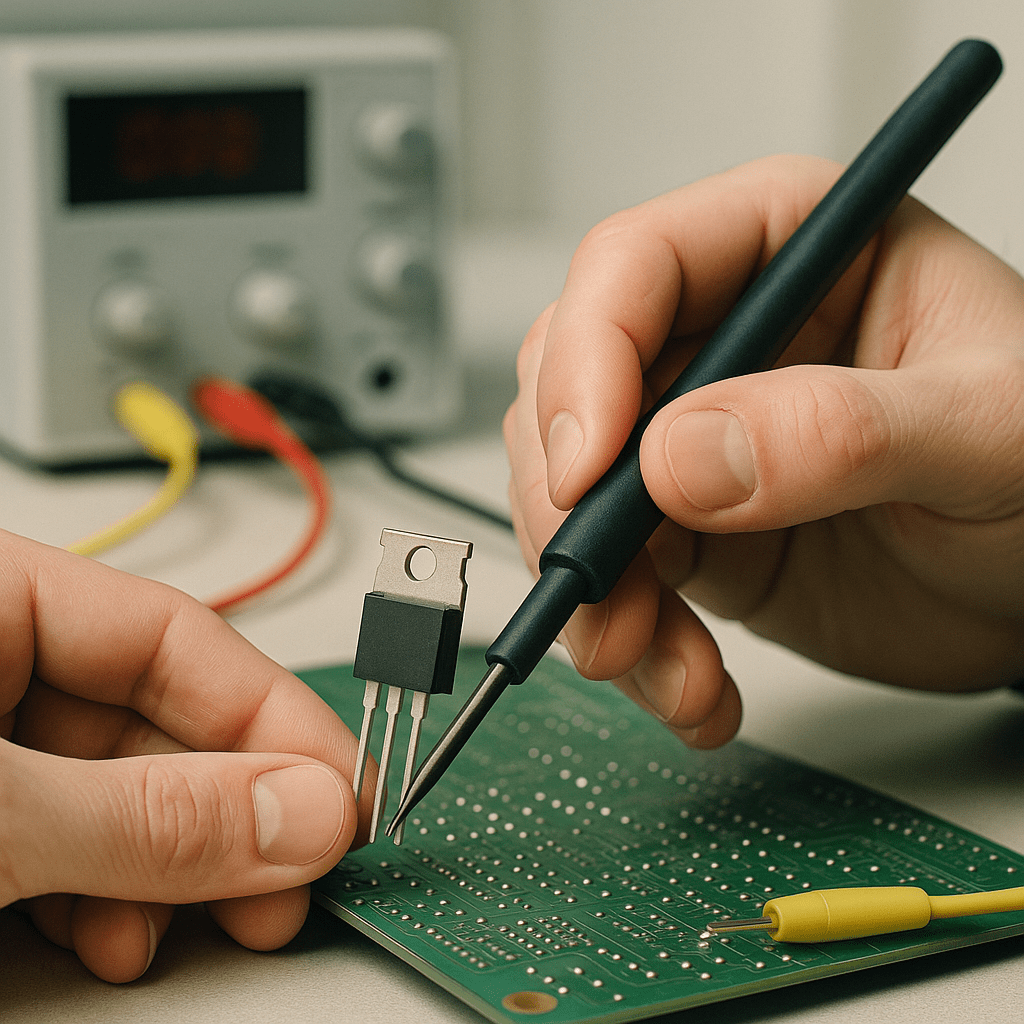
The threshold voltage, denoted VTH, is the gate‑to‑source voltage at which a MOSFET begins to conduct a noticeable amount of current. In everyday language, it is the “turn‑on” voltage of the device. Although the transition from the non‑conducting weak‑inversion region to the strongly conducting strong‑inversion region is gradual, engineers need a single, reproducible number to describe…
-
-
-
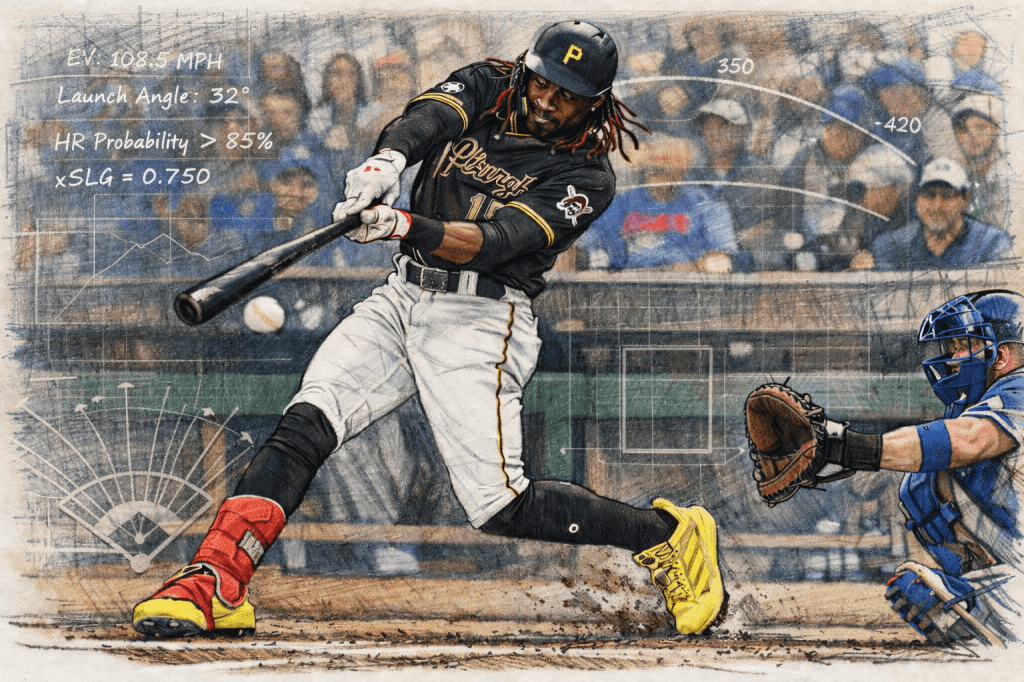
On Episode 273 of The Raw Room titled “Warheads (ft Dee Strange-Gordon)”, the two-time MLB All-Star opened up about one of the most controversial chapters of his career — his 2016 PED suspension and the narrative that surrounded it. Strange-Gordon, who won the National League batting title in 2015 with the Miami Marlins, addressed long-standing…
-
Solar cells, often called photovoltaic cells, are semiconductor devices that convert light from the sun directly into electrical energy. They form the basic building block of solar panels and many other solar power systems. Basic idea A solar cell takes incoming light, absorbs part of that light inside a semiconductor, and turns the absorbed energy…
-
Determining the threshold voltage of a MOSFET means figuring out how much gate voltage is needed before a strong conducting channel forms at the semiconductor surface. At low gate voltage the semiconductor surface is either slightly depleted or slightly accumulated and the device does not conduct much. As the gate voltage is increased the electric…
-
The MOSFET square law is an approximate rule that describes how the current through a long channel MOSFET behaves in the saturation region. In this region, once the drain voltage is high enough, the current no longer increases much with further increase in drain voltage and instead is controlled mainly by the gate voltage above…
-
MOSFETs, or Metal-Oxide-Semiconductor Field-Effect Transistors, are essential components in modern electronics, and understanding their operating characteristics is crucial for anyone interested in electronics. These devices function as switches or amplifiers, controlling the flow of electrical current. The key to their operation lies in the voltage applied to the gate terminal, which influences the conductivity between…
-
Understanding oxide charge density in semiconductors is an important concept in electronics and materials science. Semiconductors are materials that have electrical properties between those of conductors and insulators. They are essential for making electronic devices like computers and smartphones. The oxide charge density refers to the amount of electric charge that is stored in the…
-
The flatband capacitance (CFB) is defined as the total measured capacitance of a Metal-Oxide-Semiconductor (MOS) structure or a similar semiconductor device when the applied gate voltage is exactly equal to the flatband voltage VFB. This flatband voltage represents the specific potential needed to establish the flatband condition, where the energy bands within the semiconductor substrate…
-
-

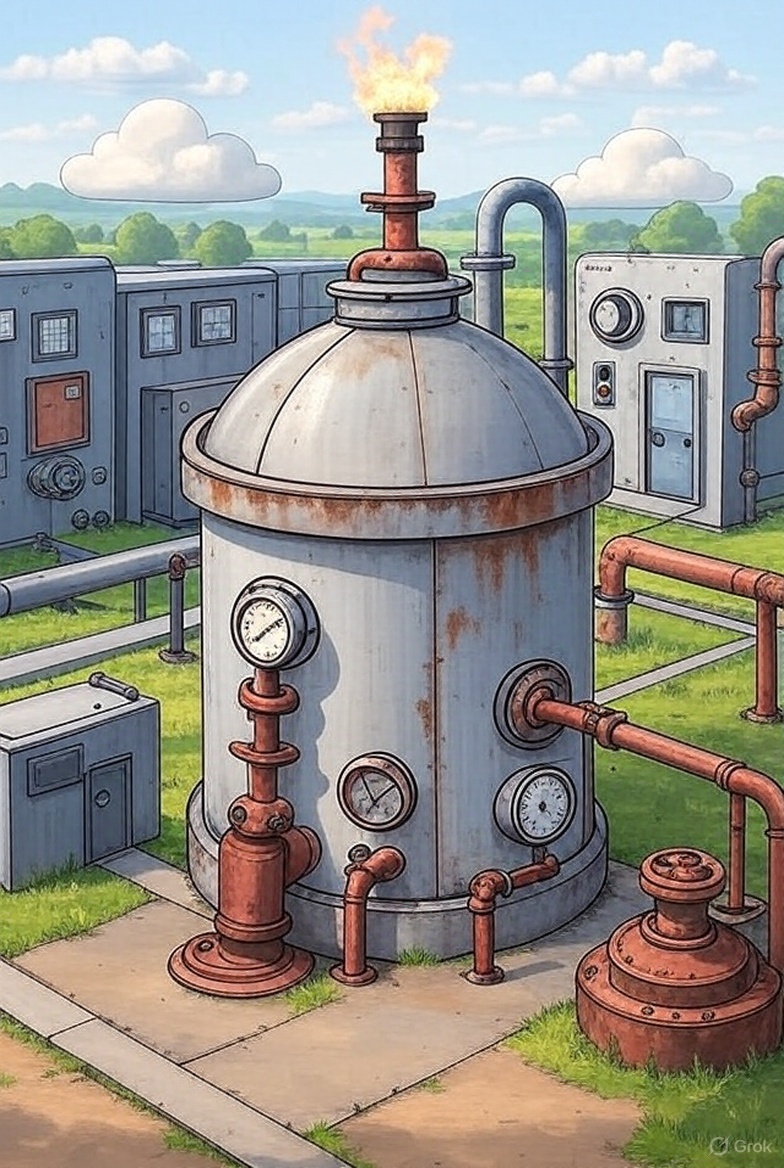
Here is a description of the three primary types of natural gas peak shaving systems: 1. LNG Peak Shaving Plants without Liquefaction Capability (Truck-Filled Plants) These facilities consist of LNG storage tanks and regasification equipment but lack on-site liquefaction capability. LNG is received by tanker trucks during periods of low demand and stored in cryogenic…
-
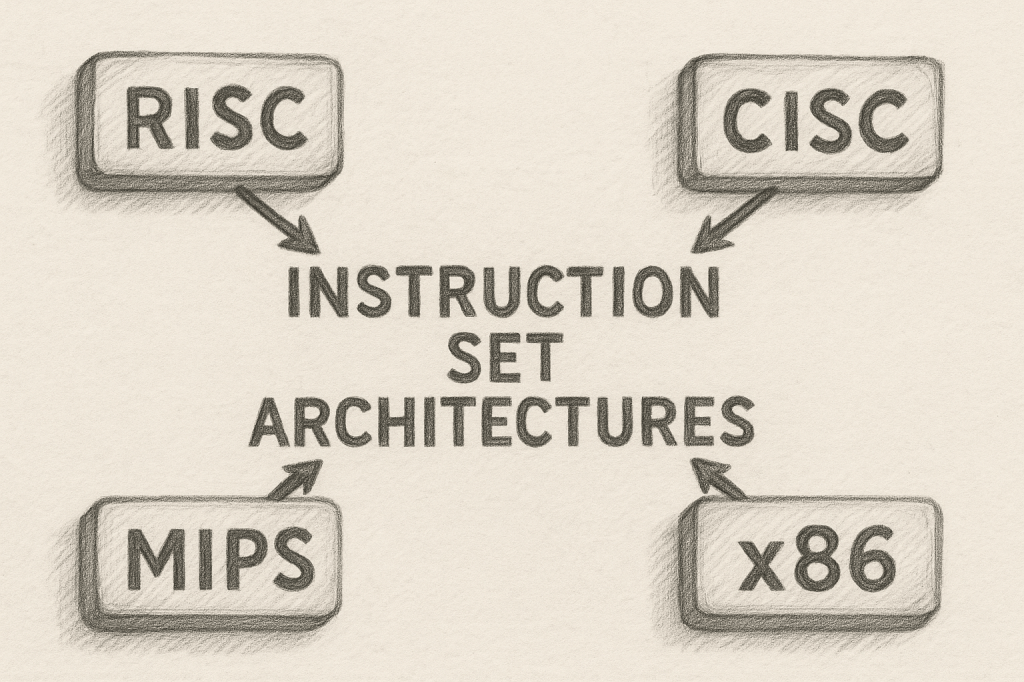
Instruction set architectures (ISAs) are crucial components of computer systems that define how software communicates with hardware. They specify the set of instructions that a processor can execute, including operations like arithmetic, data movement, and control flow. By establishing a standard interface, ISAs allow programmers to write software that can run on different hardware platforms…
-
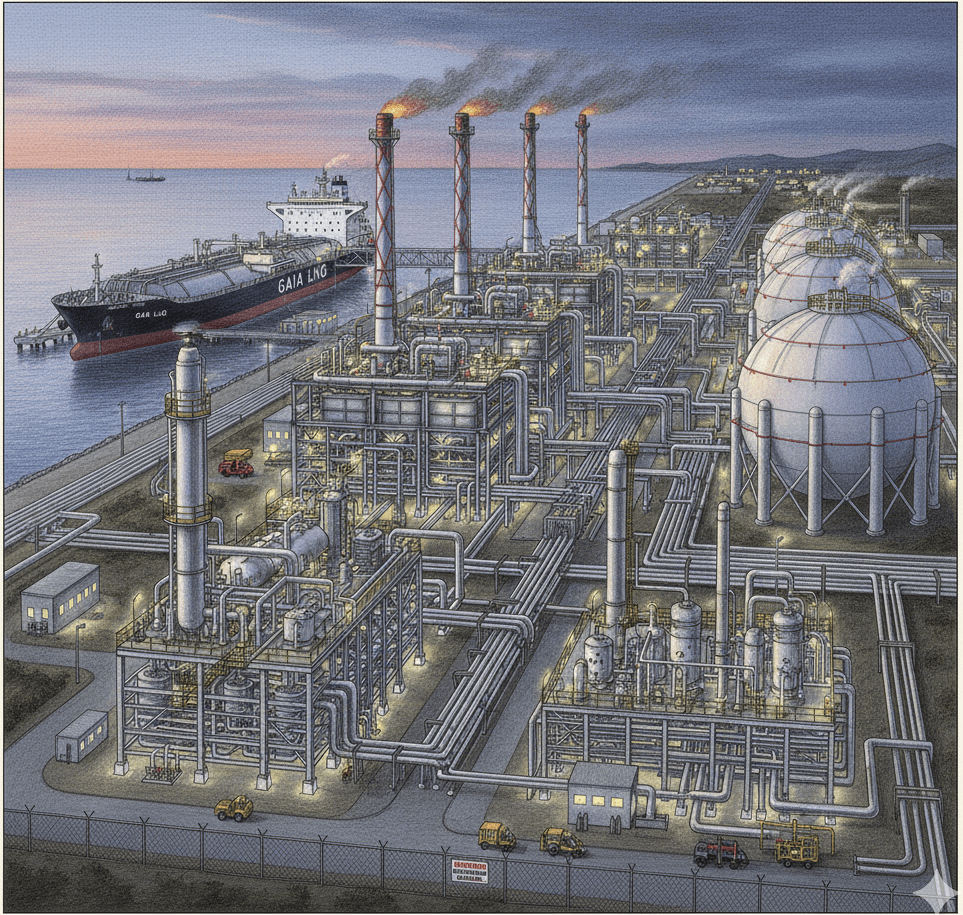
Liquefied Natural Gas (LNG) is natural gas, primarily methane, that has been converted into a liquid state by cooling it to approximately 260 degrees Fahrenheit (162 Degrees Celcius) a cryogenic process that dramatically reduces its volume to about 1/600th of its gaseous state. This enormous volume reduction makes it economically feasible and safe to transport…
-
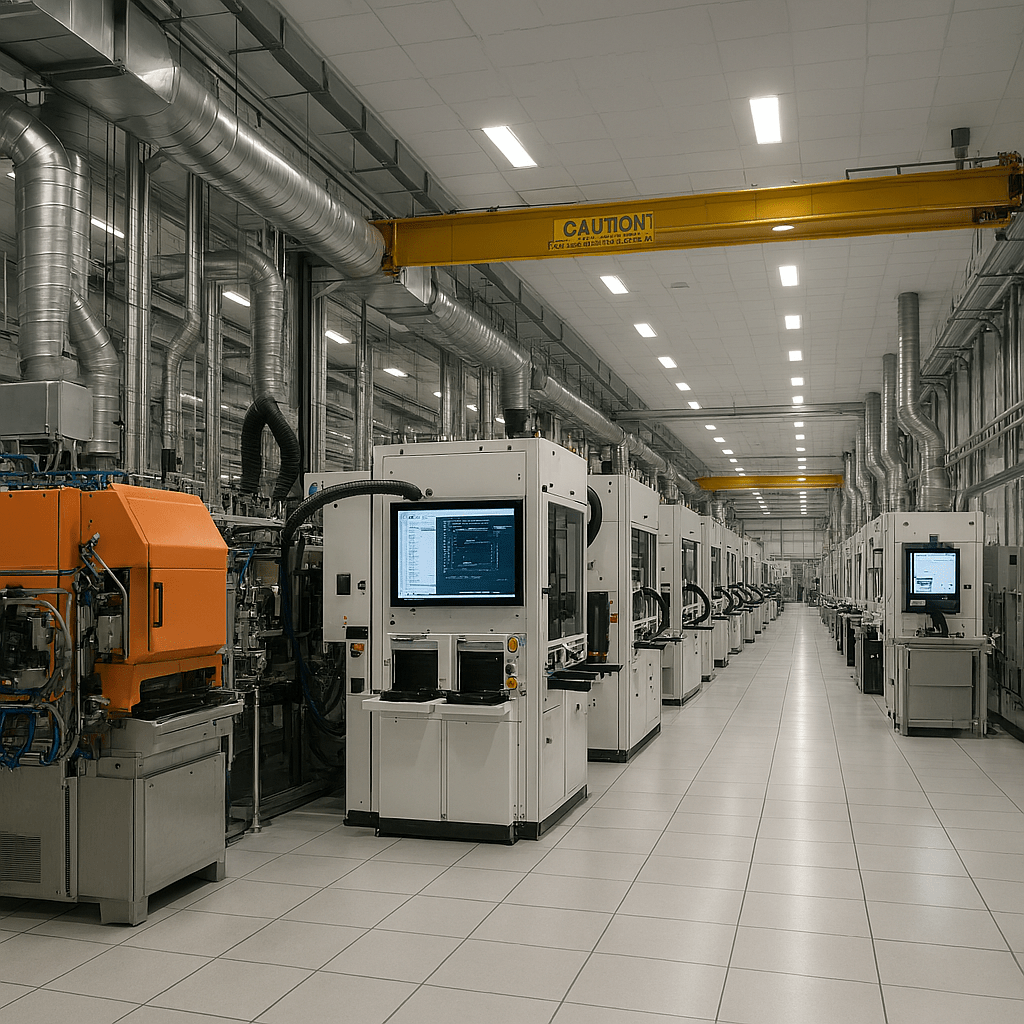
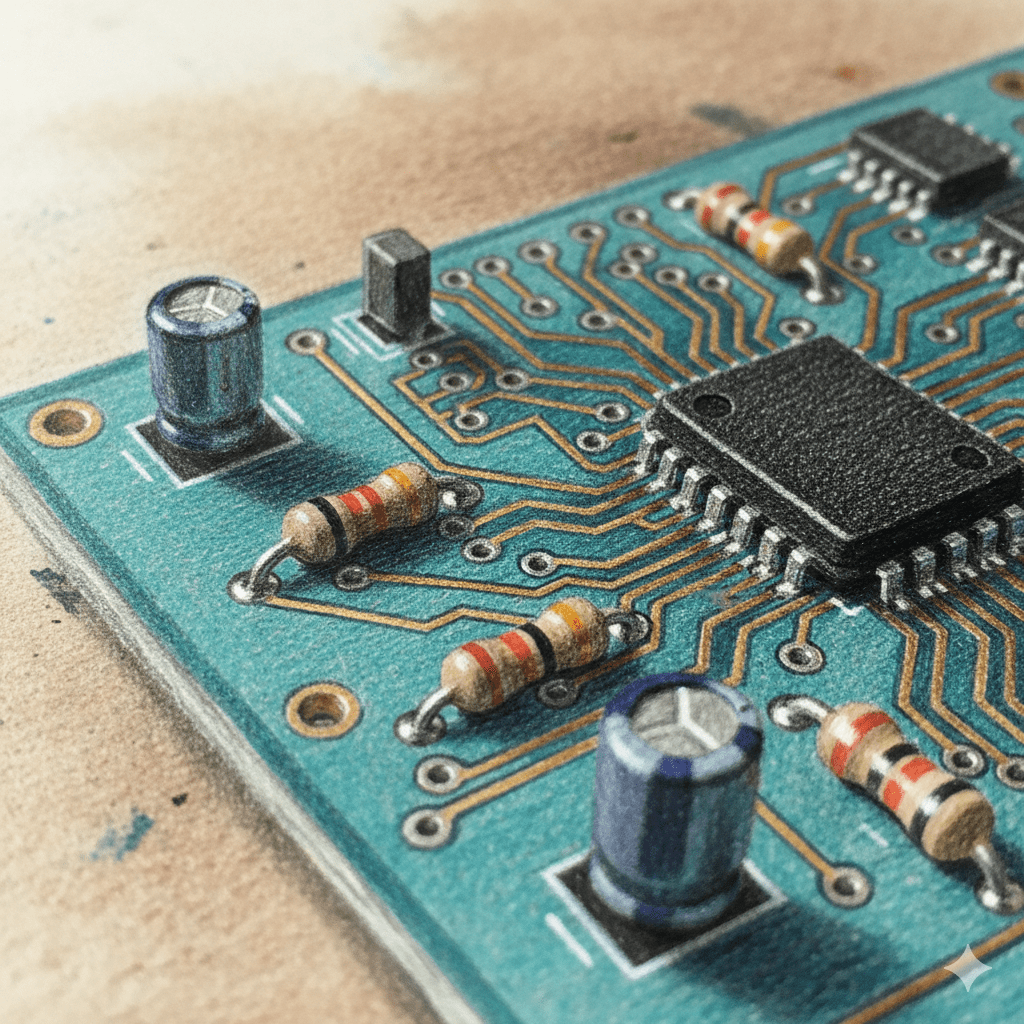
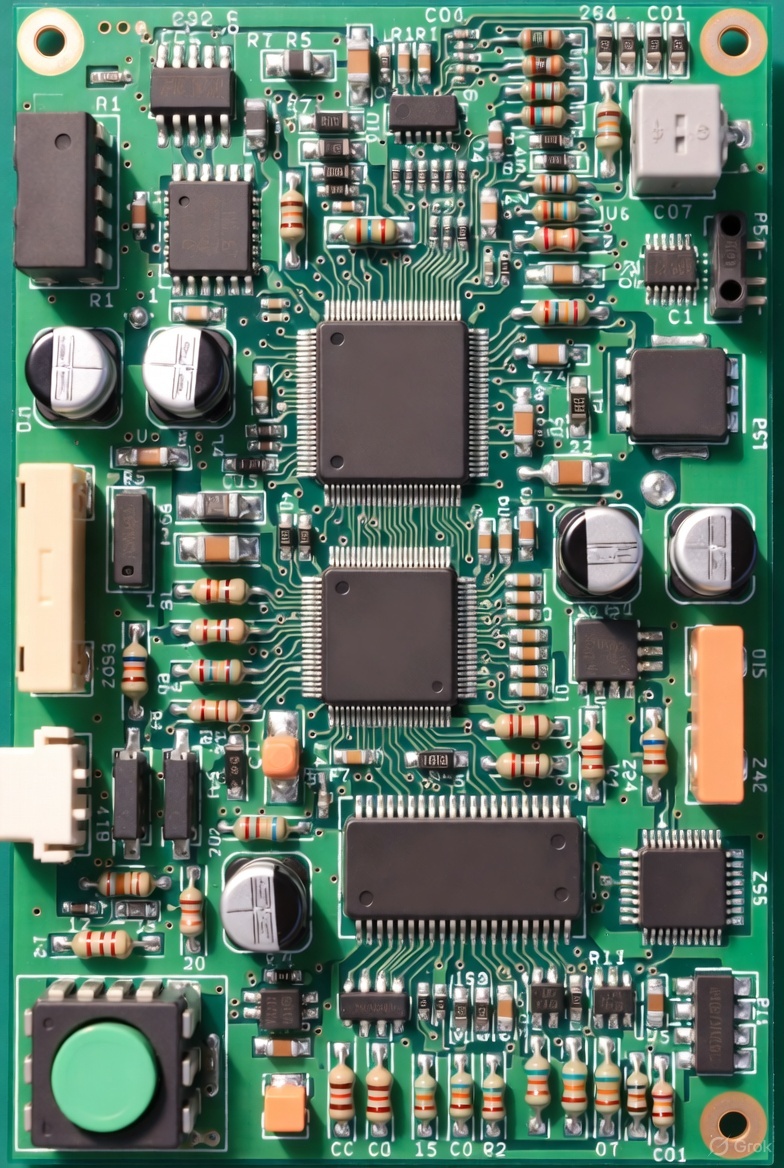
Semiconductor packaging is the stage where a bare chip is turned into a usable component that can safely live on a circuit board and inside a product. In simple terms, packaging encloses one or more semiconductor dies in a protective structure made of plastic, ceramic, glass, or metal, adds the external pins or balls that…
-

Many critics have questioned the wisdom of companies investing a significant portion of their market capitalization in Bitcoin, given its notorious volatility. However, MicroStrategy’s approach, as highlighted by Max Harvey, demonstrates a strategic advantage that might inspire other companies to follow suit.
-
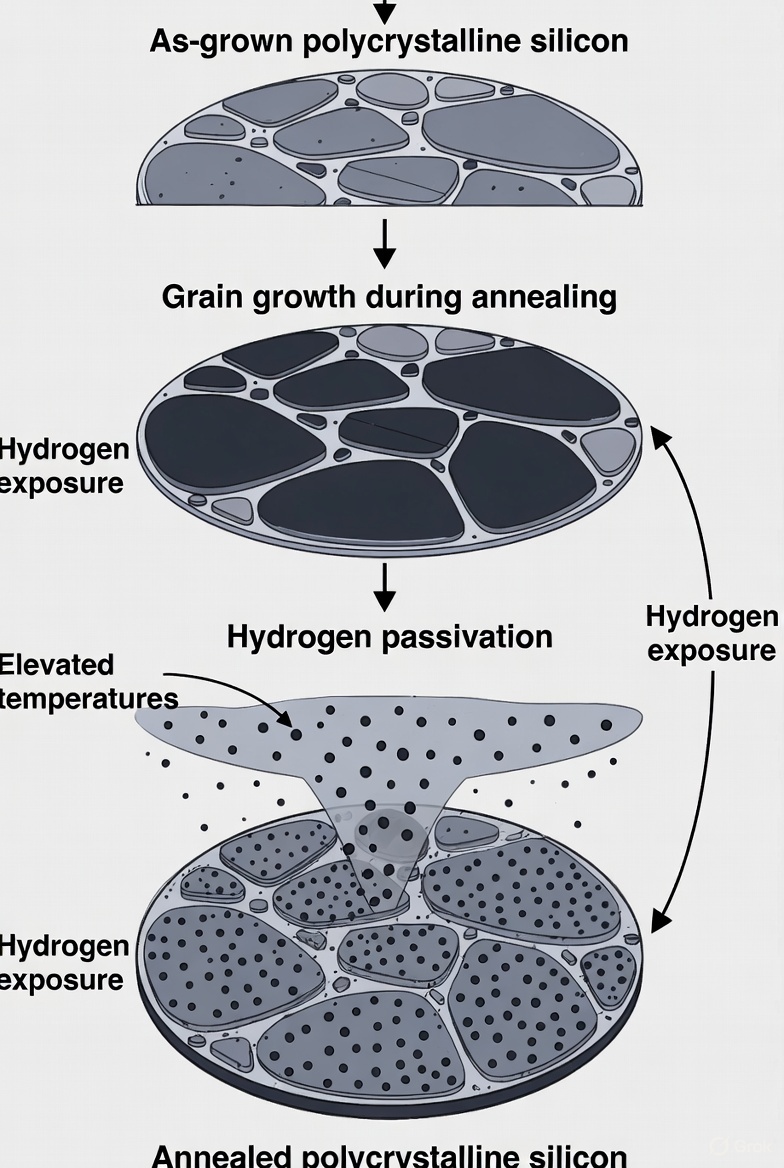
The annealing process in semiconductors is a crucial step in the manufacturing of electronic devices. This process involves heating the semiconductor material to a specific temperature and then allowing it to cool down slowly. The main purpose of annealing is to repair defects in the crystal structure of the semiconductor, which can occur during earlier…
-
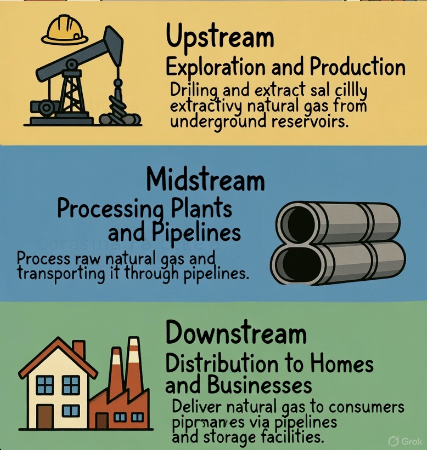
The natural gas supply chain is a complex network that involves several stages, from extraction to delivery. It begins with the exploration and drilling of natural gas wells, where companies use advanced technology to locate and extract gas from underground reservoirs. Once the gas is extracted, it is often processed to remove impurities and separate…
-
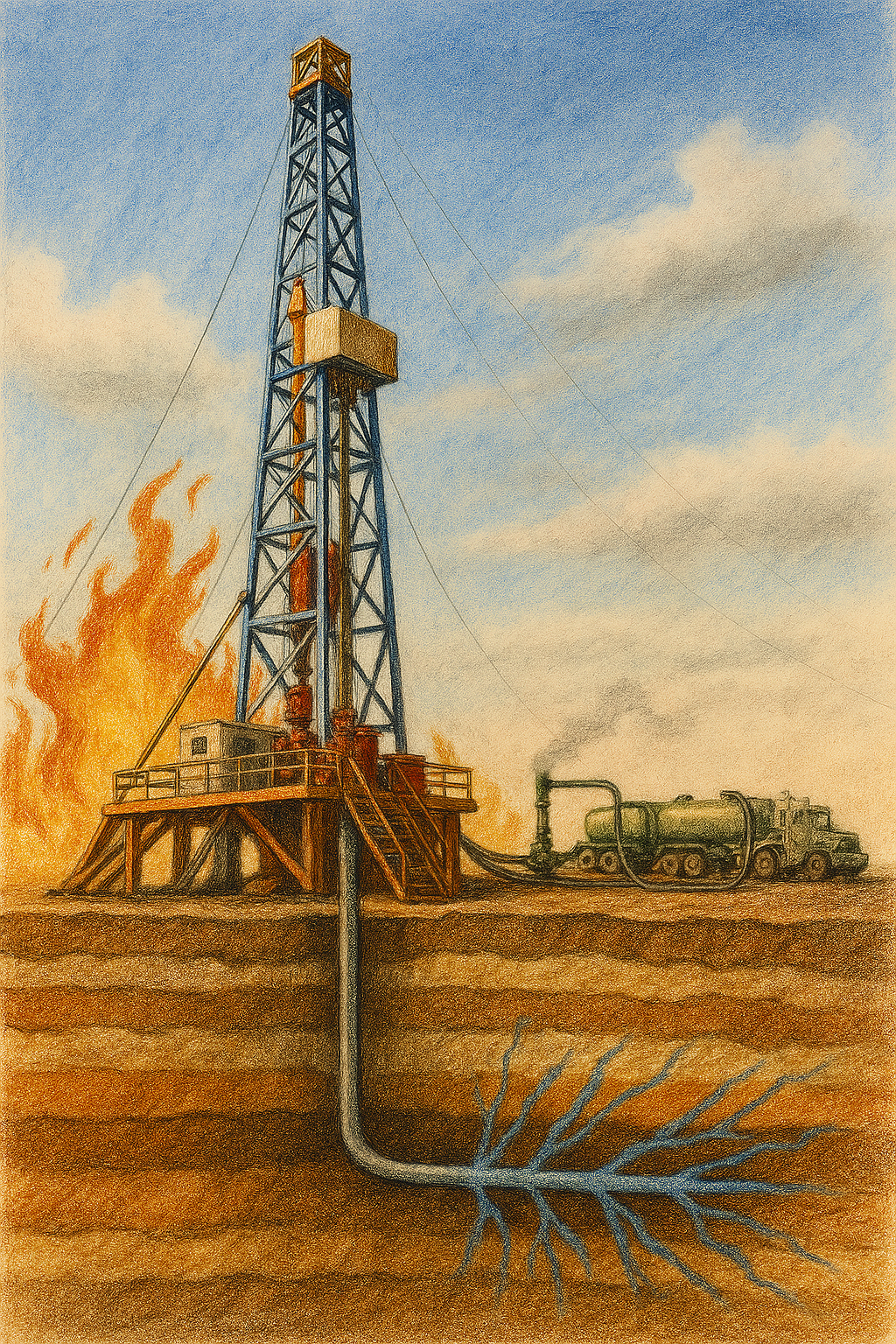
Drilling in the oil and gas industry refers to the complex, multi-stage operation of penetrating the Earth’s surface to reach underground reservoirs of hydrocarbons. It begins with site selection and permitting, followed by the deployment of a drilling rig—a towering structure equipped with rotary systems, drill bits, and support equipment. The process involves rotating a…
-
Natural gas energy refers to the energy derived from natural gas, a fossil fuel primarily composed of methane. It is a crucial component of the United States’ energy landscape, serving as a significant source of electricity generation, heating, and fuel for vehicles. Natural gas is often considered a cleaner alternative to other fossil fuels, such…
-
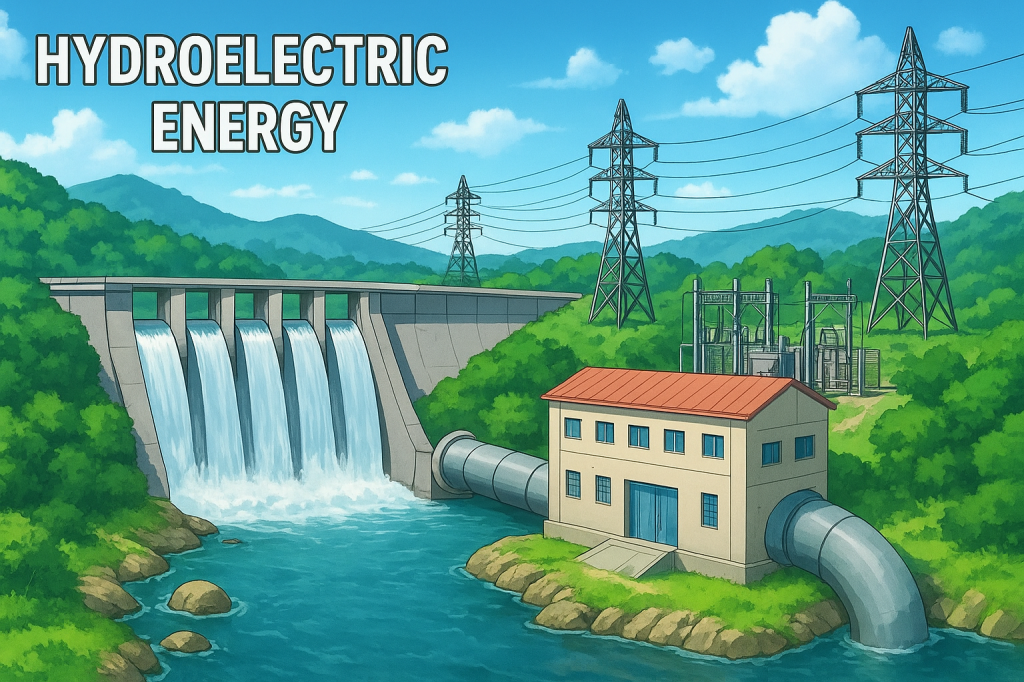
Hydroelectric energy is power produced by capturing the movement of water and converting it into electricity. Water stored in a reservoir or flowing naturally in a river passes through turbines that spin generators. This process transforms the mechanical motion of water into electrical energy through controlled and predictable operation. The system depends on gravity, flow…
-
Energy is a fundamental concept in both science and everyday life, representing the capacity to perform work or produce change. It exists in various forms, including kinetic energy, which is the energy of motion, and potential energy, which is stored energy based on an object’s position or state. For instance, a moving car possesses kinetic…
-

Solar energy is the energy that comes from the sun. It is a renewable source of energy, which means it can be used over and over again without running out. The sun produces an enormous amount of energy every day, and scientists have developed ways to capture and use this energy for various purposes. Solar…
-
The current flowing through a p-n junction diode (our one-way gate for electricity) is primarily controlled by four interacting factors. The most immediate control is the voltage applied across the diode: once the push from the battery reaches a certain minimum strength (the turn-on voltage), the current flow explodes exponentially, meaning a very small increase…